-

Lets check for Rootkit
Scan With RootKitUnHooker
- Please choose one link and download Rootkit Unhooker and save it to your desktop.
Link 1
Link 2
Link 3
- Now double-click on RKUnhookerLE.exe to run it.
- Click the Report tab, then click Scan.
- Check (Tick) Drivers and Stealth
- Uncheck the rest. then click OK
- When prompted to Select Disks for Scan, make sure C:\ is checked and click OK
- Wait till the scanner has finished and then click File > Save Report.
- Save the report somewhere where you can find it. Click Close.
- Copy the entire contents of the report and paste it in your next reply.
Note** you may get the following warning, just click OK and continue.
"Rootkit Unhooker has detected a parasite inside itself!
It is recommended to remove parasite, okay?"
-

Error loading driver, NTSTATUS code: 0xC000036B
-

I am sure these are ok but lets give them a doublecheck
You need to enable windows to show all files and folders, instructions Here
Go to VirusTotal and submit these files for analysis, just use the BROWSE feature and then Send File , you will get a report back, post the report into this thread for me to see. If the site says this file has already been checked, have them check it again
C:\Windows\SysNative\rpcnetp.exe
C:\Windows\SysWow64\rpcnetp.dll
C:\Windows\SysWow64\rpcnetp.exe
If the site is busy you can try this one
http://virusscan.jotti.org/en
-

system32\rpcnetp.exe
AhnLab-V3 2011.01.05.00 2011.01.04 -
AntiVir 7.11.1.34 2011.01.05 -
Antiy-AVL 2.0.3.7 2011.01.05 -
Avast 4.8.1351.0 2011.01.05 -
Avast5 5.0.677.0 2011.01.05 -
AVG 9.0.0.851 2011.01.05 -
BitDefender 7.2 2011.01.05 -
CAT-QuickHeal 11.00 2011.01.05 -
ClamAV 0.96.4.0 2011.01.05 -
Command 5.2.11.5 2011.01.05 -
Comodo 7302 2011.01.05 -
DrWeb 5.0.2.03300 2011.01.05 -
Emsisoft 5.1.0.1 2011.01.05 -
eSafe 7.0.17.0 2011.01.05 -
eTrust-Vet 36.1.8082 2011.01.05 -
F-Prot 4.6.2.117 2011.01.05 -
F-Secure 9.0.16160.0 2011.01.05 -
Fortinet 4.2.254.0 2011.01.05 -
GData 21 2011.01.05 -
Ikarus T3.1.1.90.0 2011.01.05 -
Jiangmin 13.0.900 2011.01.05 -
K7AntiVirus 9.75.3448 2011.01.05 -
Kaspersky 7.0.0.125 2011.01.05 -
McAfee 5.400.0.1158 2011.01.05 -
McAfee-GW-Edition 2010.1C 2011.01.05 -
Microsoft 1.6402 2011.01.05 -
NOD32 5762 2011.01.05 -
Norman 6.06.12 2011.01.05 -
nProtect 2011-01-05.01 2011.01.05 -
Panda 10.0.2.7 2011.01.05 -
PCTools 7.0.3.5 2011.01.04 -
Prevx 3.0 2011.01.05 -
Rising 22.81.02.03 2011.01.05 -
Sophos 4.60.0 2011.01.05 -
SUPERAntiSpyware 4.40.0.1006 2011.01.05 -
Symantec 20101.3.0.103 2011.01.05 -
TheHacker 6.7.0.1.110 2011.01.03 -
TrendMicro 9.120.0.1004 2011.01.05 -
TrendMicro-HouseCall 9.120.0.1004 2011.01.05 -
VBA32 3.12.14.2 2011.01.05 -
VIPRE 7964 2011.01.05 -
ViRobot 2011.1.5.4238 2011.01.05 -
VirusBuster 13.6.130.0 2011.01.05 -
Additional informationShow all
MD5 : f3d7f4487e119cc81f2593a1b5f46c60
SHA1 : a8ffe2ba597baa102363db87d0ea5973172bd842
SHA256: 454d8866efabd362514751495bd1904da35b88f460a38c86ce66a3535a0f5347
ssdeep: 384:qdzqhlwAFvItuCgq1Uko31362AhHMw5NqS5ovfEDWW:qYh/wtuCf2ko31rAtrqnvfED
File size : 17920 bytes
First seen: 2009-11-07 19:32:56
Last seen : 2011-01-05 18:31:22
TrID:
Clipper DOS Executable (33.5%)
Generic Win/DOS Executable (33.2%)
DOS Executable Generic (33.2%)
sigcheck:
publisher....: n/a
copyright....: n/a
product......: n/a
description..: n/a
original name: n/a
internal name: n/a
file version.: n/a
comments.....: n/a
signers......: -
signing date.: -
verified.....: Unsigned
PEInfo: PE structure information
[[ basic data ]]
entrypointaddress: 0x2D33
timedatestamp....: 0x4AA64AA6 (Tue Sep 08 12:14:30 2009)
machinetype......: 0x14c (I386)
[[ 4 section(s) ]]
name, viradd, virsiz, rawdsiz, ntropy, md5
.text, 0x1000, 0x3656, 0x3800, 6.28, bd5f969a91fc3d21288a7cc2eff0973f
.data, 0x5000, 0x1B0, 0x200, 0.44, add2dea5f5d22802d5094bfb9a1c2d66
.cdata, 0x6000, 0x23C, 0x400, 1.38, 73024c065a38cff8621719054485aad7
.reloc, 0x7000, 0x344, 0x400, 5.86, ddc2acf91f7cf7147d7b05373b85d064
[[ 5 import(s) ]]
ADVAPI32.dll: RegQueryValueExA, DuplicateTokenEx, CreateProcessAsUserA, RegisterServiceCtrlHandlerA, RegOpenKeyA, RegCloseKey, RegDeleteValueA, StartServiceCtrlDispatcherA, RegEnumValueA, SetServiceStatus, OpenProcessToken, SetTokenInformation
KERNEL32.dll: LocalAlloc, VirtualAllocEx, FreeLibrary, SetThreadPriority, SetStdHandle, GetVersion, RtlUnwind, LoadLibraryA, ResumeThread, CreateProcessA, LocalFree, CloseHandle, VirtualFreeEx, ReadFile, EnterCriticalSection, CreateFileA, TerminateProcess, lstrlenA, GetStdHandle, GetCurrentThreadId, GetSystemDirectoryA, OpenProcess, GetCurrentProcessId, SetEvent, LeaveCriticalSection, CreateEventA, GetOverlappedResult, GetLastError, ExitThread, CreateThread, WriteProcessMemory, ExitProcess, GetModuleHandleA, GetProcAddress, lstrcatA, ReadProcessMemory, lstrcmpiA, DeleteCriticalSection, WaitForSingleObject, CreateRemoteThread, WriteFile, InitializeCriticalSection, WaitForMultipleObjects, lstrcpyA, RaiseException, CopyFileA, TerminateThread, GetModuleFileNameA, GetExitCodeThread, SetFilePointer, ResetEvent, Sleep
USER32.dll: KillTimer, PostMessageA, GetMessageA, TranslateMessage, CreateWindowExA, RegisterClassA, DispatchMessageA, PostThreadMessageA, PostQuitMessage, DefWindowProcA, wsprintfA, SetTimer, PeekMessageA
WSOCK32.dll: -, -, -, -
USERENV.dll: CreateEnvironmentBlock
[[ 1 export(s) ]]
rpcnetp
ExifTool:
file metadata
Error: File format error
FileSize: 18 kB
Symantec reputation:Suspicious.Insight
sysWOW64\rpcnetp.dll
0 VT Community user(s) with a total of 0 reputation credit(s) say(s) this sample is goodware. 0 VT Community user(s) with a total of 0 reputation credit(s) say(s) this sample is malware.
File name: rpcnetp.dll
Submission date: 2011-01-05 18:23:46 (UTC)
Current status: finished
Result: 0/ 43 (0.0%)
VT Community
not reviewed
Safety score: -
Compact
Print results
Antivirus Version Last Update Result
AhnLab-V3 2011.01.05.00 2011.01.04 -
AntiVir 7.11.1.34 2011.01.05 -
Antiy-AVL 2.0.3.7 2011.01.05 -
Avast 4.8.1351.0 2011.01.05 -
Avast5 5.0.677.0 2011.01.05 -
AVG 9.0.0.851 2011.01.05 -
BitDefender 7.2 2011.01.05 -
CAT-QuickHeal 11.00 2011.01.05 -
ClamAV 0.96.4.0 2011.01.05 -
Command 5.2.11.5 2011.01.05 -
Comodo 7302 2011.01.05 -
DrWeb 5.0.2.03300 2011.01.05 -
Emsisoft 5.1.0.1 2011.01.05 -
eSafe 7.0.17.0 2011.01.05 -
eTrust-Vet 36.1.8082 2011.01.05 -
F-Prot 4.6.2.117 2011.01.05 -
F-Secure 9.0.16160.0 2011.01.05 -
Fortinet 4.2.254.0 2011.01.05 -
GData 21 2011.01.05 -
Ikarus T3.1.1.90.0 2011.01.05 -
Jiangmin 13.0.900 2011.01.05 -
K7AntiVirus 9.75.3448 2011.01.05 -
Kaspersky 7.0.0.125 2011.01.05 -
McAfee 5.400.0.1158 2011.01.05 -
McAfee-GW-Edition 2010.1C 2011.01.05 -
Microsoft 1.6402 2011.01.05 -
NOD32 5762 2011.01.05 -
Norman 6.06.12 2011.01.05 -
nProtect 2011-01-05.01 2011.01.05 -
Panda 10.0.2.7 2011.01.05 -
PCTools 7.0.3.5 2011.01.04 -
Prevx 3.0 2011.01.05 -
Rising 22.81.02.03 2011.01.05 -
Sophos 4.60.0 2011.01.05 -
SUPERAntiSpyware 4.40.0.1006 2011.01.05 -
Symantec 20101.3.0.103 2011.01.05 -
TheHacker 6.7.0.1.110 2011.01.03 -
TrendMicro 9.120.0.1004 2011.01.05 -
TrendMicro-HouseCall 9.120.0.1004 2011.01.05 -
VBA32 3.12.14.2 2011.01.05 -
VIPRE 7964 2011.01.05 -
ViRobot 2011.1.5.4238 2011.01.05 -
VirusBuster 13.6.130.0 2011.01.05 -
Additional informationShow all
MD5 : 29edfb09b08085b80d2715b4eaff97f5
SHA1 : 7277ea315ad82d99358fc5a311686b1857b9f126
SHA256: 0a48fd481cc5901b6a1608b58e55823d77cef5bd2897392f201a450af301292e
ssdeep: 384:KdzqhlwAFvItuCgq1Uko31362AhHMw5NqS5ovfEDWW:KYh/wtuCf2ko31rAtrqnvfED
File size : 17920 bytes
First seen: 2009-10-26 15:49:16
Last seen : 2011-01-05 18:23:46
TrID:
Clipper DOS Executable (33.5%)
Generic Win/DOS Executable (33.2%)
DOS Executable Generic (33.2%)
sigcheck:
publisher....: n/a
copyright....: n/a
product......: n/a
description..: n/a
original name: n/a
internal name: n/a
file version.: n/a
comments.....: n/a
signers......: -
signing date.: -
verified.....: Unsigned
PEInfo: PE structure information
[[ basic data ]]
entrypointaddress: 0x2D33
timedatestamp....: 0x4AA64AA6 (Tue Sep 08 12:14:30 2009)
machinetype......: 0x14c (I386)
[[ 4 section(s) ]]
name, viradd, virsiz, rawdsiz, ntropy, md5
.text, 0x1000, 0x3656, 0x3800, 6.28, bd5f969a91fc3d21288a7cc2eff0973f
.data, 0x5000, 0x1B0, 0x200, 0.44, add2dea5f5d22802d5094bfb9a1c2d66
.cdata, 0x6000, 0x23C, 0x400, 1.38, 73024c065a38cff8621719054485aad7
.reloc, 0x7000, 0x344, 0x400, 5.86, ddc2acf91f7cf7147d7b05373b85d064
[[ 5 import(s) ]]
ADVAPI32.dll: RegQueryValueExA, DuplicateTokenEx, CreateProcessAsUserA, RegisterServiceCtrlHandlerA, RegOpenKeyA, RegCloseKey, RegDeleteValueA, StartServiceCtrlDispatcherA, RegEnumValueA, SetServiceStatus, OpenProcessToken, SetTokenInformation
KERNEL32.dll: LocalAlloc, VirtualAllocEx, FreeLibrary, SetThreadPriority, SetStdHandle, GetVersion, RtlUnwind, LoadLibraryA, ResumeThread, CreateProcessA, LocalFree, CloseHandle, VirtualFreeEx, ReadFile, EnterCriticalSection, CreateFileA, TerminateProcess, lstrlenA, GetStdHandle, GetCurrentThreadId, GetSystemDirectoryA, OpenProcess, GetCurrentProcessId, SetEvent, LeaveCriticalSection, CreateEventA, GetOverlappedResult, GetLastError, ExitThread, CreateThread, WriteProcessMemory, ExitProcess, GetModuleHandleA, GetProcAddress, lstrcatA, ReadProcessMemory, lstrcmpiA, DeleteCriticalSection, WaitForSingleObject, CreateRemoteThread, WriteFile, InitializeCriticalSection, WaitForMultipleObjects, lstrcpyA, RaiseException, CopyFileA, TerminateThread, GetModuleFileNameA, GetExitCodeThread, SetFilePointer, ResetEvent, Sleep
USER32.dll: KillTimer, PostMessageA, GetMessageA, TranslateMessage, CreateWindowExA, RegisterClassA, DispatchMessageA, PostThreadMessageA, PostQuitMessage, DefWindowProcA, wsprintfA, SetTimer, PeekMessageA
WSOCK32.dll: -, -, -, -
USERENV.dll: CreateEnvironmentBlock
[[ 1 export(s) ]]
rpcnetp
ExifTool:
file metadata
Error: File format error
FileSize: 18 kB
Symantec reputation:Suspicious.Insight
SysWOw64\rpcnetp.exe
0 VT Community user(s) with a total of 0 reputation credit(s) say(s) this sample is goodware. 0 VT Community user(s) with a total of 0 reputation credit(s) say(s) this sample is malware.
File name: rpcnetp.exe
Submission date: 2011-01-05 18:26:21 (UTC)
Current status: finished
Result: 0/ 42 (0.0%)
VT Community
not reviewed
Safety score: -
Compact
Print results
Antivirus Version Last Update Result
AhnLab-V3 2011.01.05.00 2011.01.04 -
AntiVir 7.11.1.34 2011.01.05 -
Antiy-AVL 2.0.3.7 2011.01.05 -
Avast 4.8.1351.0 2011.01.05 -
Avast5 5.0.677.0 2011.01.05 -
AVG 9.0.0.851 2011.01.05 -
BitDefender 7.2 2011.01.05 -
CAT-QuickHeal 11.00 2011.01.05 -
ClamAV 0.96.4.0 2011.01.05 -
Command 5.2.11.5 2011.01.05 -
Comodo 7302 2011.01.05 -
DrWeb 5.0.2.03300 2011.01.05 -
Emsisoft 5.1.0.1 2011.01.05 -
eSafe 7.0.17.0 2011.01.05 -
eTrust-Vet 36.1.8082 2011.01.05 -
F-Prot 4.6.2.117 2011.01.05 -
F-Secure 9.0.16160.0 2011.01.05 -
Fortinet 4.2.254.0 2011.01.05 -
GData 21 2011.01.05 -
Ikarus T3.1.1.90.0 2011.01.05 -
Jiangmin 13.0.900 2011.01.05 -
K7AntiVirus 9.75.3448 2011.01.05 -
Kaspersky 7.0.0.125 2011.01.05 -
McAfee 5.400.0.1158 2011.01.05 -
McAfee-GW-Edition 2010.1C 2011.01.05 -
Microsoft 1.6402 2011.01.05 -
NOD32 5762 2011.01.05 -
Norman 6.06.12 2011.01.05 -
nProtect 2011-01-05.01 2011.01.05 -
Panda 10.0.2.7 2011.01.05 -
PCTools 7.0.3.5 2011.01.04 -
Prevx 3.0 2011.01.05 -
Rising 22.81.02.03 2011.01.05 -
Sophos 4.60.0 2011.01.05 -
SUPERAntiSpyware 4.40.0.1006 2011.01.05 -
TheHacker 6.7.0.1.110 2011.01.03 -
TrendMicro 9.120.0.1004 2011.01.05 -
TrendMicro-HouseCall 9.120.0.1004 2011.01.05 -
VBA32 3.12.14.2 2011.01.05 -
VIPRE 7964 2011.01.05 -
ViRobot 2011.1.5.4238 2011.01.05 -
VirusBuster 13.6.130.0 2011.01.05 -
Additional informationShow all
MD5 : f3d7f4487e119cc81f2593a1b5f46c60
SHA1 : a8ffe2ba597baa102363db87d0ea5973172bd842
SHA256: 454d8866efabd362514751495bd1904da35b88f460a38c86ce66a3535a0f5347
ssdeep: 384:qdzqhlwAFvItuCgq1Uko31362AhHMw5NqS5ovfEDWW:qYh/wtuCf2ko31rAtrqnvfED
File size : 17920 bytes
First seen: 2009-11-07 19:32:56
Last seen : 2011-01-05 18:26:21
TrID:
Clipper DOS Executable (33.5%)
Generic Win/DOS Executable (33.2%)
DOS Executable Generic (33.2%)
sigcheck:
publisher....: n/a
copyright....: n/a
product......: n/a
description..: n/a
original name: n/a
internal name: n/a
file version.: n/a
comments.....: n/a
signers......: -
signing date.: -
verified.....: Unsigned
PEInfo: PE structure information
[[ basic data ]]
entrypointaddress: 0x2D33
timedatestamp....: 0x4AA64AA6 (Tue Sep 08 12:14:30 2009)
machinetype......: 0x14c (I386)
[[ 4 section(s) ]]
name, viradd, virsiz, rawdsiz, ntropy, md5
.text, 0x1000, 0x3656, 0x3800, 6.28, bd5f969a91fc3d21288a7cc2eff0973f
.data, 0x5000, 0x1B0, 0x200, 0.44, add2dea5f5d22802d5094bfb9a1c2d66
.cdata, 0x6000, 0x23C, 0x400, 1.38, 73024c065a38cff8621719054485aad7
.reloc, 0x7000, 0x344, 0x400, 5.86, ddc2acf91f7cf7147d7b05373b85d064
[[ 5 import(s) ]]
ADVAPI32.dll: RegQueryValueExA, DuplicateTokenEx, CreateProcessAsUserA, RegisterServiceCtrlHandlerA, RegOpenKeyA, RegCloseKey, RegDeleteValueA, StartServiceCtrlDispatcherA, RegEnumValueA, SetServiceStatus, OpenProcessToken, SetTokenInformation
KERNEL32.dll: LocalAlloc, VirtualAllocEx, FreeLibrary, SetThreadPriority, SetStdHandle, GetVersion, RtlUnwind, LoadLibraryA, ResumeThread, CreateProcessA, LocalFree, CloseHandle, VirtualFreeEx, ReadFile, EnterCriticalSection, CreateFileA, TerminateProcess, lstrlenA, GetStdHandle, GetCurrentThreadId, GetSystemDirectoryA, OpenProcess, GetCurrentProcessId, SetEvent, LeaveCriticalSection, CreateEventA, GetOverlappedResult, GetLastError, ExitThread, CreateThread, WriteProcessMemory, ExitProcess, GetModuleHandleA, GetProcAddress, lstrcatA, ReadProcessMemory, lstrcmpiA, DeleteCriticalSection, WaitForSingleObject, CreateRemoteThread, WriteFile, InitializeCriticalSection, WaitForMultipleObjects, lstrcpyA, RaiseException, CopyFileA, TerminateThread, GetModuleFileNameA, GetExitCodeThread, SetFilePointer, ResetEvent, Sleep
USER32.dll: KillTimer, PostMessageA, GetMessageA, TranslateMessage, CreateWindowExA, RegisterClassA, DispatchMessageA, PostThreadMessageA, PostQuitMessage, DefWindowProcA, wsprintfA, SetTimer, PeekMessageA
WSOCK32.dll: -, -, -, -
USERENV.dll: CreateEnvironmentBlock
[[ 1 export(s) ]]
rpcnetp
ExifTool:
file metadata
Error: File format error
FileSize: 18 kB
-

Those files are fine
See if you can run this program, if it wont run you can try it in safemode
To Enter Safemode
- Go to Start> Shut off your Computer> Restart
- As the computer starts to boot-up, Tap the F8 KEY somewhat rapidly,
this will bring up a menu. - Use the Up and Down Arrow Keys to scroll up to Safemode with Networking
- Then press the Enter Key on your Keyboard
Tutorial if you need it How to boot into Safemode
Download ComboFix from one of these locations:
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools
- See this Link for programs that need to be disabled and instruction on how to disable them.
- Remember to re-enable them when we're done.
- Double click on ComboFix.exe & follow the prompts.
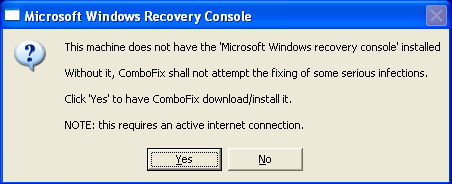
- As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
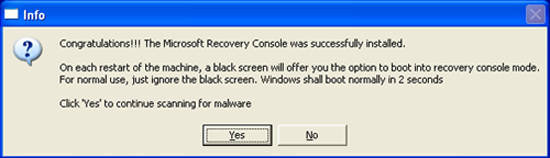
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
*If there is no internet connection when Combofix has completely finished then restart your computer to restore back the connections.
-

ComboFix 11-01-05.02 - TheEarl 01/05/2011 22:40:22.1.2 - x64
Microsoft Windows 7 Professional 6.1.7600.0.1252.1.1033.18.4091.2905 [GMT -6:00]
Running from: c:\users\TheEarl\Desktop\ComboFix.exe
FW: ZoneAlarm Firewall *Disabled* {D17DF357-CFF5-F001-D1C1-FCD21DFE3D5E}
SP: Windows Defender *Enabled/Updated* {D68DDC3A-831F-4fae-9E44-DA132C1ACF46}
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
C:\Install.exe
c:\users\TheEarl\AppData\Local\Microsoft\Windows\Temporary Internet Files\www.leawo.com_favicon.ico
c:\users\TheEarl\AppData\Local\Microsoft\Windows\Temporary Internet Files\www.lepak.tv_favicon.ico
c:\users\TheEarl\AppData\Local\Microsoft\Windows\Temporary Internet Files\www.youtube.com_favicon.ico
.
((((((((((((((((((((((((( Files Created from 2010-12-06 to 2011-01-06 )))))))))))))))))))))))))))))))
.
2011-01-06 04:46 . 2011-01-06 04:46 -------- d-----w- c:\users\postgres\AppData\Local\temp
2011-01-06 04:46 . 2011-01-06 04:46 -------- d-----w- c:\users\Default\AppData\Local\temp
2011-01-05 17:44 . 2011-01-05 18:38 34560 ----a-w- c:\windows\SysWow64\drivers\Normandy.sys
2011-01-05 07:09 . 2011-01-05 07:09 -------- d-----w- c:\users\TheEarl\AppData\Local\Bit.Trip Beat
2011-01-05 04:42 . 2010-02-04 16:01 238936 ----a-w- c:\windows\SysWow64\xactengine3_6.dll
2011-01-05 04:42 . 2010-02-04 16:01 22360 ----a-w- c:\windows\SysWow64\X3DAudio1_7.dll
2011-01-05 04:37 . 2011-01-05 04:42 -------- d--h--w- c:\windows\msdownld.tmp
2011-01-05 04:24 . 2011-01-05 04:24 -------- d-----w- c:\users\TheEarl\AppData\Roaming\Beat Hazard
2011-01-05 00:57 . 2011-01-05 00:57 -------- d-----w- c:\program files (x86)\ESET
2010-12-31 19:47 . 2010-12-31 19:47 -------- d-----w- c:\users\TheEarl\AppData\Local\Apple
2010-12-31 19:47 . 2010-12-31 19:47 -------- d-----w- c:\users\TheEarl\AppData\Local\Apple Computer
2010-12-31 15:36 . 2010-12-31 15:36 -------- d-----w- c:\users\TheEarl\AppData\Local\Adobe
2010-12-31 15:28 . 2010-12-21 00:09 38224 ----a-w- c:\windows\SysWow64\drivers\mbamswissarmy.sys
2010-12-31 15:23 . 2010-11-16 18:01 8199504 ----a-w- c:\programdata\Microsoft\Windows Defender\Definition Updates\{DD004638-4AB4-4635-804F-0A04160E4B15}\mpengine.dll
2010-12-27 21:45 . 2011-01-02 04:33 215128 ----a-w- c:\windows\SysWow64\PnkBstrB.xtr
2010-12-27 21:45 . 2010-12-27 21:45 -------- d-----w- c:\users\TheEarl\AppData\Local\PunkBuster
2010-12-25 03:07 . 2010-12-25 03:07 -------- d-----w- c:\users\TheEarl\AppData\Local\Windows Live
2010-12-25 03:07 . 2010-12-25 03:07 -------- d-----w- c:\program files (x86)\Common Files\Windows Live
2010-12-25 03:06 . 2010-05-23 10:15 1619456 ----a-w- c:\windows\SysWow64\WMVDECOD.DLL
2010-12-25 03:06 . 2010-05-23 10:11 196608 ----a-w- c:\windows\SysWow64\mfreadwrite.dll
2010-12-25 03:06 . 2010-05-23 10:11 3181568 ----a-w- c:\windows\SysWow64\mf.dll
2010-12-25 03:05 . 2010-10-19 08:47 7680 ----a-w- c:\program files\Internet Explorer\iecompat.dll
2010-12-25 03:05 . 2010-10-19 08:10 7680 ----a-w- c:\program files (x86)\Internet Explorer\iecompat.dll
2010-12-25 03:05 . 2010-01-18 23:29 85504 ----a-w- c:\windows\SysWow64\secproc_ssp_isv.dll
2010-12-25 03:05 . 2010-01-18 23:29 85504 ----a-w- c:\windows\SysWow64\secproc_ssp.dll
2010-12-25 03:05 . 2010-01-18 23:29 365568 ----a-w- c:\windows\SysWow64\secproc_isv.dll
2010-12-25 03:05 . 2010-01-18 23:29 369152 ----a-w- c:\windows\SysWow64\secproc.dll
2010-12-25 03:05 . 2010-01-18 23:28 324608 ----a-w- c:\windows\SysWow64\RMActivate_isv.exe
2010-12-25 03:05 . 2010-01-18 23:28 277504 ----a-w- c:\windows\SysWow64\RMActivate_ssp_isv.exe
2010-12-25 03:05 . 2010-01-18 23:28 320512 ----a-w- c:\windows\SysWow64\RMActivate.exe
2010-12-25 03:05 . 2010-01-18 23:28 280064 ----a-w- c:\windows\SysWow64\RMActivate_ssp.exe
2010-12-16 22:40 . 2010-11-16 23:45 69120 ----a-w- c:\windows\SysWow64\zlcomm.dll
2010-12-16 22:40 . 2010-11-16 23:45 104448 ----a-w- c:\windows\SysWow64\zlcommdb.dll
2010-12-16 22:40 . 2010-12-16 22:40 -------- d-----w- c:\windows\SysWow64\ZoneLabs
2010-12-16 22:40 . 2010-11-16 23:45 1238528 ----a-w- c:\windows\SysWow64\zpeng25.dll
2010-12-16 22:40 . 2010-12-16 22:40 -------- d-----w- c:\program files (x86)\Zone Labs
2010-12-09 16:39 . 2011-01-06 04:23 17920 ----a-w- c:\windows\SysWow64\rpcnetp.dll
2010-12-09 16:39 . 2011-01-06 04:23 17920 ----a-w- c:\windows\SysWow64\rpcnetp.exe
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2011-01-06 04:23 . 2010-01-08 21:39 57752 ----a-w- c:\windows\SysWow64\rpcnet.dll
2010-12-06 18:19 . 2010-12-06 18:19 11336456 ----a-w- c:\programdata\Tempmozy-update-a31217e595a1463492ad999467f8f0a1.exe
2010-11-14 02:39 . 2010-01-17 04:32 340 ----a-w- c:\windows\wininit.tmp
2010-11-13 00:53 . 2010-05-01 06:39 472808 ----a-w- c:\windows\SysWow64\deployJava1.dll
2010-10-14 07:36 . 2010-10-14 07:36 15451288 ----a-w- c:\windows\SysWow64\xlive.dll
2010-10-14 07:36 . 2010-10-14 07:36 13642904 ----a-w- c:\windows\SysWow64\xlivefnt.dll
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Google Update"="c:\users\TheEarl\AppData\Local\Google\Update\GoogleUpdate.exe" [2010-01-09 135664]
"ISUSPM Startup"="c:\progra~2\COMMON~1\INSTAL~1\UPDATE~1\ISUSPM.exe" [2006-09-11 218032]
"ISUSPM"="c:\program files (x86)\Common Files\InstallShield\UpdateService\ISUSPM.exe" [2006-09-11 218032]
"Steam"="c:\program files (x86)\Steam\Steam.exe" [2010-11-25 1242448]
"RockMelt Update"="c:\users\TheEarl\AppData\Local\RockMelt\Update\RockMeltUpdate.exe" [2010-11-26 136336]
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
"OEM13Mon.exe"="c:\windows\OEM13Mon.exe" [2008-01-07 36864]
"PDVDDXSrv"="c:\program files (x86)\CyberLink\PowerDVD DX\PDVDDXSrv.exe" [2009-02-05 128232]
"SSBkgdUpdate"="c:\program files (x86)\Common Files\Scansoft Shared\SSBkgdUpdate\SSBkgdupdate.exe" [2006-10-25 210472]
"ISUSScheduler"="c:\program files (x86)\Common Files\InstallShield\UpdateService\issch.exe" [2008-10-24 79136]
"DNS7reminder"="c:\program files (x86)\Nuance\NaturallySpeaking10\Ereg\Ereg.exe" [2007-04-16 259624]
"GrooveMonitor"="c:\program files (x86)\Microsoft Office\Office12\GrooveMonitor.exe" [2008-10-25 31072]
"SunJavaUpdateSched"="c:\program files (x86)\Common Files\Java\Java Update\jusched.exe" [2010-05-14 248552]
"DivXUpdate"="c:\program files (x86)\DivX\DivX Update\DivXUpdate.exe" [2010-09-01 1164584]
"Adobe Reader Speed Launcher"="c:\program files (x86)\Adobe\Reader 9.0\Reader\Reader_sl.exe" [2010-09-23 35760]
"Adobe ARM"="c:\program files (x86)\Common Files\Adobe\ARM\1.0\AdobeARM.exe" [2010-09-21 932288]
"QuickTime Task"="c:\program files (x86)\QuickTime\QTTask.exe" [2010-09-08 421888]
"iTunesHelper"="c:\program files (x86)\iTunes\iTunesHelper.exe" [2010-11-18 421160]
"ZoneAlarm Client"="c:\program files (x86)\Zone Labs\ZoneAlarm\zlclient.exe" [2010-11-16 1043968]
c:\programdata\Microsoft\Windows\Start Menu\Programs\Startup\
MozyHome Status.lnk - c:\program files (x86)\Mozy\mozystat.exe [2010-11-8 4832056]
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\policies\system]
"ConsentPromptBehaviorAdmin"= 5 (0x5)
"ConsentPromptBehaviorUser"= 3 (0x3)
"EnableUIADesktopToggle"= 0 (0x0)
[HKEY_LOCAL_MACHINE\software\wow6432node\microsoft\windows nt\currentversion\drivers32]
"aux2"=wdmaud.drv
[HKEY_LOCAL_MACHINE\system\currentcontrolset\control\session manager]
BootExecute REG_MULTI_SZ autocheck autochk /p \??\C:\0autocheck autochk *
[HKEY_LOCAL_MACHINE\system\currentcontrolset\control\lsa]
Security Packages REG_MULTI_SZ kerberos msv1_0 schannel wdigest tspkg pku2u livessp
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\Wdf01000.sys]
@="Driver"
R2 clr_optimization_v4.0.30319_32;Microsoft .NET Framework NGEN v4.0.30319_X86;c:\windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe [2010-03-18 130384]
R2 clr_optimization_v4.0.30319_64;Microsoft .NET Framework NGEN v4.0.30319_X64;c:\windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe [2010-03-18 138576]
R2 gupdate;Google Update Service (gupdate);c:\program files (x86)\Google\Update\GoogleUpdate.exe [2010-11-29 136176]
R3 B-Service;B-Service;c:\users\TheEarl\AppData\Roaming\Mikogo\B-Service.exe [2010-10-07 185640]
R3 dc3d;MS Hardware Device Detection Driver (HID);c:\windows\system32\DRIVERS\dc3d.sys [2009-11-04 22528]
R3 evserial;Virtual Serial Ports Driver (Eltima Softwate);c:\windows\system32\DRIVERS\evserial.sys [2008-05-19 67072]
R3 Normandy;Normandy SR2; [x]
R3 USBAAPL64;Apple Mobile USB Driver;c:\windows\system32\Drivers\usbaapl64.sys [2010-09-28 51712]
R3 VSBC;Virtual Serial Bus Enumerator (Eltima Software);c:\windows\system32\DRIVERS\evsbc.sys [2008-05-19 32768]
R3 WatAdminSvc;Windows Activation Technologies Service;c:\windows\system32\Wat\WatAdminSvc.exe [2010-02-25 1255736]
S0 DLACDBHE;DLACDBHE;c:\windows\System32\Drivers\DLACDBHE.SYS [2007-07-23 17776]
S0 DRVECDB;DRVECDB;c:\windows\System32\Drivers\DRVECDB.SYS [2007-07-23 124112]
S0 PxHlpa64;PxHlpa64;c:\windows\System32\Drivers\PxHlpa64.sys [2010-08-12 55856]
S1 DLARTL_E;DLARTL_E;c:\windows\system32\Drivers\DLARTL_E.SYS [2007-07-23 41072]
S1 vwififlt;Virtual WiFi Filter Driver;c:\windows\system32\DRIVERS\vwififlt.sys [2009-07-14 59904]
S2 DLABMFSE;DLABMFSE;c:\windows\system32\Drivers\DLABMFSE.SYS [2007-07-23 46448]
S2 DLABOIOE;DLABOIOE;c:\windows\system32\Drivers\DLABOIOE.SYS [2007-07-23 42352]
S2 DLADResE;DLADResE;c:\windows\system32\Drivers\DLADResE.SYS [2007-07-23 9968]
S2 DLAIFS_E;DLAIFS_E;c:\windows\system32\Drivers\DLAIFS_E.SYS [2007-07-23 146672]
S2 DLAOPIOE;DLAOPIOE;c:\windows\system32\Drivers\DLAOPIOE.SYS [2007-07-23 35056]
S2 DLAPoolE;DLAPoolE;c:\windows\system32\Drivers\DLAPoolE.SYS [2007-07-23 19824]
S2 DLAUDF_E;DLAUDF_E;c:\windows\system32\Drivers\DLAUDF_E.SYS [2007-07-23 144112]
S2 DLAUDFAE;DLAUDFAE;c:\windows\system32\Drivers\DLAUDFAE.SYS [2007-07-23 135152]
S2 DRVEDDM;DRVEDDM;c:\windows\system32\Drivers\DRVEDDM.SYS [2007-07-23 63984]
S2 postgresql-8.4;PostgreSQL Server 8.4;C:/Program Files (x86)/PostgreSQL/8.4/bin/pg_ctl.exe runservice -N postgresql-8.4 -D C:/Program Files (x86)/PostgreSQL/8.4/data -w [x]
S3 btusbflt;Bluetooth USB Filter;c:\windows\system32\drivers\btusbflt.sys [2010-04-14 54824]
S3 OEM13Vfx;Creative Camera OEM013 Video VFX Driver;c:\windows\system32\DRIVERS\OEM13Vfx.sys [2007-03-05 12288]
S3 OEM13Vid;Creative Camera OEM013 Driver;c:\windows\system32\DRIVERS\OEM13Vid.sys [2008-05-28 267296]
S3 RTL8167;Realtek 8167 NT Driver;c:\windows\system32\DRIVERS\Rt64win7.sys [2010-06-23 344680]
S3 vwifimp;Microsoft Virtual WiFi Miniport Service;c:\windows\system32\DRIVERS\vwifimp.sys [2009-07-14 17920]
.
Contents of the 'Scheduled Tasks' folder
2011-01-06 c:\windows\Tasks\GoogleUpdateTaskMachineCore.job
- c:\program files (x86)\Google\Update\GoogleUpdate.exe [2010-11-29 00:24]
2011-01-06 c:\windows\Tasks\GoogleUpdateTaskMachineUA.job
- c:\program files (x86)\Google\Update\GoogleUpdate.exe [2010-11-29 00:24]
2011-01-06 c:\windows\Tasks\GoogleUpdateTaskUserS-1-5-21-4210094983-2902076926-636801332-1001Core.job
- c:\users\TheEarl\AppData\Local\Google\Update\GoogleUpdate.exe [2010-01-09 00:40]
2011-01-06 c:\windows\Tasks\GoogleUpdateTaskUserS-1-5-21-4210094983-2902076926-636801332-1001UA.job
- c:\users\TheEarl\AppData\Local\Google\Update\GoogleUpdate.exe [2010-01-09 00:40]
2011-01-01 c:\windows\Tasks\NatSpeak Periodic Acoustic Optimization.job
- c:\program files (x86)\Nuance\NaturallySpeaking10\Program\schedmgr.exe [2009-03-17 01:45]
2011-01-05 c:\windows\Tasks\NatSpeak Periodic Language Model Optimization.job
- c:\program files (x86)\Nuance\NaturallySpeaking10\Program\schedmgr.exe [2009-03-17 01:45]
2011-01-05 c:\windows\Tasks\RockMeltUpdateTaskUserS-1-5-21-4210094983-2902076926-636801332-1001Core.job
- c:\users\TheEarl\AppData\Local\RockMelt\Update\RockMeltUpdate.exe [2010-11-26 05:03]
2011-01-06 c:\windows\Tasks\RockMeltUpdateTaskUserS-1-5-21-4210094983-2902076926-636801332-1001UA.job
- c:\users\TheEarl\AppData\Local\RockMelt\Update\RockMeltUpdate.exe [2010-11-26 05:03]
.
--------- x86-64 -----------
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\explorer\shelliconoverlayidentifiers\mozy2]
@="{747E722C-CB46-4a9d-BDFE-192AAD5099B1}"
[HKEY_CLASSES_ROOT\CLSID\{747E722C-CB46-4a9d-BDFE-192AAD5099B1}]
2010-11-08 22:06 4345144 ----a-w- c:\program files (x86)\Mozy\mozyshell.dll
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\explorer\shelliconoverlayidentifiers\mozy3]
@="{EE6F5A00-7898-40f7-AB77-51FF9D6DEB20}"
[HKEY_CLASSES_ROOT\CLSID\{EE6F5A00-7898-40f7-AB77-51FF9D6DEB20}]
2010-11-08 22:06 4345144 ----a-w- c:\program files (x86)\Mozy\mozyshell.dll
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Apoint"="c:\program files\DellTPad\Apoint.exe" [2009-06-29 309248]
"NvCplDaemon"="c:\windows\system32\NvCpl.dll" [2009-06-11 16328736]
"NVHotkey"="c:\windows\system32\nvHotkey.dll" [2009-06-11 93728]
"Windows Mobile Device Center"="c:\windows\WindowsMobile\wmdc.exe" [2007-05-31 660360]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows]
"LoadAppInit_DLLs"=0x1
.
------- Supplementary Scan -------
.
uLocal Page = c:\windows\system32\blank.htm
uStart Page = https://share.law.northwestern.edu/jclc/default.aspx
mLocal Page = c:\windows\SysWOW64\blank.htm
uInternet Settings,ProxyOverride = *.local
IE: E&xport to Microsoft Excel - c:\progra~2\MICROS~2\Office12\EXCEL.EXE/3000
.
- - - - ORPHANS REMOVED - - - -
AddRemove-PunkBusterSvc - c:\windows\system32\pbsvc_bc2.exe
[HKEY_LOCAL_MACHINE\system\ControlSet001\services\postgresql-8.4]
"ImagePath"="C:/Program Files (x86)/PostgreSQL/8.4/bin/pg_ctl.exe runservice -N \"postgresql-8.4\" -D \"C:/Program Files (x86)/PostgreSQL/8.4/data\" -w"
[HKEY_LOCAL_MACHINE\system\ControlSet001\services\postgresql-8.4]
"ImagePath"="C:/Program Files (x86)/PostgreSQL/8.4/bin/pg_ctl.exe runservice -N \"postgresql-8.4\" -D \"C:/Program Files (x86)/PostgreSQL/8.4/data\" -w"
.
--------------------- LOCKED REGISTRY KEYS ---------------------
[HKEY_USERS\S-1-5-21-4210094983-2902076926-636801332-1001\Software\SecuROM\License information*]
"datasecu"=hex:46,fb,21,13,39,81,62,09,5a,e6,45,32,f7,6e,33,e7,cc,d1,27,36,e0,
7c,13,30,60,97,7e,8c,46,77,09,c7,60,10,69,d1,66,ef,60,e1,85,24,7f,5e,e4,e2,\
"rkeysecu"=hex:2f,0f,d5,3e,02,2b,06,63,b1,0b,dd,b6,71,e2,54,98
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\Windows\\SysWOW64\\Macromed\\Flash\\FlashUtil10k_ActiveX.exe,-101"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\Elevation]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\LocalServer32]
@="c:\\Windows\\SysWOW64\\Macromed\\Flash\\FlashUtil10k_ActiveX.exe"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}]
@Denied: (A 2) (Everyone)
@="Shockwave Flash Object"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}\InprocServer32]
@="c:\\Windows\\SysWOW64\\Macromed\\Flash\\Flash10k.ocx"
"ThreadingModel"="Apartment"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}\MiscStatus]
@="0"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}\ProgID]
@="ShockwaveFlash.ShockwaveFlash.10"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}\ToolboxBitmap32]
@="c:\\Windows\\SysWOW64\\Macromed\\Flash\\Flash10k.ocx, 1"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}\TypeLib]
@="{D27CDB6B-AE6D-11cf-96B8-444553540000}"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}\Version]
@="1.0"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB6E-AE6D-11cf-96B8-444553540000}\VersionIndependentProgID]
@="ShockwaveFlash.ShockwaveFlash"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB70-AE6D-11cf-96B8-444553540000}]
@Denied: (A 2) (Everyone)
@="Macromedia Flash Factory Object"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB70-AE6D-11cf-96B8-444553540000}\InprocServer32]
@="c:\\Windows\\SysWOW64\\Macromed\\Flash\\Flash10k.ocx"
"ThreadingModel"="Apartment"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB70-AE6D-11cf-96B8-444553540000}\ProgID]
@="FlashFactory.FlashFactory.1"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB70-AE6D-11cf-96B8-444553540000}\ToolboxBitmap32]
@="c:\\Windows\\SysWOW64\\Macromed\\Flash\\Flash10k.ocx, 1"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB70-AE6D-11cf-96B8-444553540000}\TypeLib]
@="{D27CDB6B-AE6D-11cf-96B8-444553540000}"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB70-AE6D-11cf-96B8-444553540000}\Version]
@="1.0"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\CLSID\{D27CDB70-AE6D-11cf-96B8-444553540000}\VersionIndependentProgID]
@="FlashFactory.FlashFactory"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}]
@Denied: (A 2) (Everyone)
@="IFlashBroker4"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
[HKEY_LOCAL_MACHINE\software\Classes\Wow6432Node\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
[HKEY_LOCAL_MACHINE\software\Microsoft\Cryptography\RNG*]
"Seed"=hex:49,31,f4,88,04,28,01,14,c5,ca,fa,5f,f5,cf,66,6e,1f,6c,42,48,3b,1d,
bb,84,6e,c3,98,a3,07,68,b8,a1,8e,3f,71,ca,a8,53,6d,af,a8,e5,29,51,a3,e5,99,\
[HKEY_LOCAL_MACHINE\software\Wow6432Node\Microsoft\Windows CE Services]
"SymbolicLinkValue"=hex(6):5c,00,72,00,65,00,67,00,69,00,73,00,74,00,72,00,79,
00,5c,00,4d,00,41,00,43,00,48,00,49,00,4e,00,45,00,5c,00,53,00,4f,00,46,00,\
[HKEY_LOCAL_MACHINE\system\ControlSet001\Control\PCW\Security]
@Denied: (Full) (Everyone)
.
Completion time: 2011-01-05 22:56:35
ComboFix-quarantined-files.txt 2011-01-06 04:56
Pre-Run: 74,523,205,632 bytes free
Post-Run: 75,613,544,448 bytes free
- - End Of File - - FDAB5B6825CFFE7820F306B78D4D5018
-

Not to much removed. How are things running now ?
-

Haven't had a blue screen of death, but programs still acting up. Tried reinstalling photoshop (one of the programs consistently freezing) but no change. Chkdsk still won't work either. :(
-

Hi,
http://forums.whatthetech.com/index.php?showforum=119
All us forums work together, why don't you post here for your windows problems and see if they can help you. If they feel its still malware related post back and we can dig deeper. You can link them to this thread so they can see what we have done.
Ken
-
 Posting Permissions
Posting Permissions
- You may not post new threads
- You may not post replies
- You may not post attachments
- You may not edit your posts
-
Forum Rules