-
 Unknown Problem and it's bad
Unknown Problem and it's bad
I am not sure about doing anything, because I don't know if my computer will be able to boot back up.
The Problem(s)
About 10 days ago my primary desktop (up to date McAfee, Malwarebytes & Spybot) was in the process of re-booting itself (I didn't reboot it).
However, during the boot-up the process stopped,
and the screen to choose the last known 'good' config or safe mode appeared.
The computer would not boot-up, even in safe mode.
Didn't fix the primary computer because I was going to using a newer back-up computer but doesn't have all the programs as the primary.
A couple of days ago, the back-up computer started doing the exact same thing and stopped the same place in the boot process and couldn't be booted up in normal mode. However, the back-up computer could be booted up in safe mode without networking.
Malware found 1 virus. After the fix and after multiple attempts, the computer finally booted up in normal mode.
But. it booted up with a modified Browser window that I had never seen before and icons on the desktop, "Launch White Smoke translator" and "Buy White Smoke translator" that I had never installed nor seen before.
With computer able to connect to the internet, I updated Malwarebytes and re-ran it. Over 800 viruses/Malware were found with most being White Smoke intrusions.
However, 2 are Trojan.Agent "6to4v32.dll" and "certstore.dat".
I haven't removed the infections because I presume that a re-boot will be necessary, and I am not sure if the computer will be boot up again.
Also, didn't know if some type of boot up disc needs to be made.
I would guess whatever has infected the back-up computer is also the cause of the primary computer's issues as well.
Please advise.
Thanks for your help.
FlaCajun
-


Please read Before You Post
While best efforts are made to assist in removing infections safely, unexpected stuff can happen. It is advisable that you back up your important data before starting any clean up procedure. Neither Safer Networking Forums nor the Analyst providing the advice may be held responsible for any loss.
Until we deem your system clean I am going to ask you not to install or uninstall any software or hardware except for the programs we may run.
Just so you know we only work on one computer at a time or it gets very confusing. We can work on your primary computer and when where done this thread will be closed and then you can post for the second one. If both computers are experiencing the same thing I would suggest that your router is infected. What I would do is to unplug your back up computer from the internet and turn the computer off. Then reset your router, there generally is a little pin hole on the back that a paper clip can slip in , hold it in for about 10 seconds or so, then you will have to setup your router.
After you do that run this program and post the log
Download DDS from one of the links below to your desktop
Link 1
Link 2
- Double click the tool to run it.
- A black Screen will open, just read the contents and do nothing.
- When the tool finishes, it will open 2 reports, DDS.txt and attach.txt
- Copy/Paste the contents of 'DDS.txt' into your post.
- 'attach.txt' should be zipped using Windows native zip utility and attached to your post. Compress and uncompress files (zip files)
-

I am going to work on the secondary computer first, unless otherwise instructed. It has booted up in regular mode, but cannot connect to the internet.
The primary computer doesn't boot up even in safe mode.
(note: I purchased a Spybot start-up disc this past week).
The files on the secondary computer have been backed up.
I will be using a laptop to down load the files suggested
and transfer the results via flash drive.
The laptop security programs are updated (McAfee, Malwarebytes, Spybot)
and the flash drive will be scanned prior to any activity.
Also, Malwarebytes has found over 800 virus files, most of them White Smoke
with 2 trojans. But, the removal of the programs has not been executed awaiting your instructions.
I will get you the DDS files.
Thanks.
-

If you already ran Malwarebytes, open it and go into the Reports tab and copy and paste the report for me to see.
Then go ahead and run DDS and post the log
-

Here is the Malwarebytes log.
DDS log to follow.
It was too long so I zipped the file.
I uploaded the file using the paper clip attachment.
It has been scanned for viruses.
Don't know if it worked.
-

DDS Log and Attach.txt
DDS (Ver_10-12-12.02) - NTFSx86
Run by Raymond Green at 23:47:15.04 on Sat 12/18/2010
Internet Explorer: 7.0.5730.11
============== Running Processes ===============
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\Explorer.EXE
C:\WINDOWS\system32\spoolsv.exe
C:\Program Files\CyberLink\PowerDVD\PDVDServ.exe
C:\Program Files\Java\jre1.6.0_05\bin\jusched.exe
C:\Acer\Empowering Technology\eDataSecurity\eDSloader.exe
C:\WINDOWS\RTHDCPL.EXE
C:\Acer\Empowering Technology\eRecovery\eRAgent.exe
C:\Program Files\Microsoft IntelliType Pro\itype.exe
C:\Program Files\Microsoft IntelliPoint\ipoint.exe
C:\Program Files\McAfee.com\Agent\mcagent.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\ATI Technologies\ATI.ACE\CLI.EXE
C:\PROGRA~1\McAfee\MSC\mcmscsvc.exe
c:\program files\common files\mcafee\mna\mcnasvc.exe
c:\PROGRA~1\COMMON~1\mcafee\mcproxy\mcproxy.exe
C:\PROGRA~1\McAfee\VIRUSS~1\mcshield.exe
C:\WINDOWS\system32\wscntfy.exe
C:\WINDOWS\System32\alg.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\PROGRA~1\McAfee\VIRUSS~1\mcsysmon.exe
C:\Program Files\Java\jre1.6.0_05\bin\jucheck.exe
C:\Program Files\Adobe\Reader 8.0\Reader\AcroRd32.exe
C:\Program Files\Malwarebytes' Anti-Malware\mbam.exe
C:\PROGRA~1\McAfee\MSM\McSmtFwk.exe
C:\PROGRA~1\COMMON~1\McAfee\MSC\McUICnt.exe
c:\PROGRA~1\mcafee\msc\mcupdmgr.exe
C:\WINDOWS\system32\sol.exe
C:\WINDOWS\system32\NOTEPAD.EXE
C:\Documents and Settings\Raymond Green\Desktop\dds.scr
C:\WINDOWS\system32\svchost.exe -k NetworkService
C:\WINDOWS\system32\svchost.exe -k LocalService
C:\WINDOWS\System32\svchost.exe -k netsvcs
C:\WINDOWS\system32\svchost.exe -k imgsvc
============== Pseudo HJT Report ===============
uStart Page = hxxp://www.kitco.com/
uSearch Page = hxxp://us.rd.yahoo.com/customize/ycomp/defaults/sp/*http://www.yahoo.com
uSearch Bar = hxxp://www.comcast.net/toolbar2.0/search/
uSearchMigratedDefaultURL = hxxp://search.yahoo.com/search?p={searchTerms}&ei=utf-8&fr=b1ie7
uSearchURL,(Default) = hxxp://us.rd.yahoo.com/customize/ycomp/defaults/su/*http://www.yahoo.com
mSearchAssistant = hxxp://www.comcast.net/toolbar2.0/search/
uURLSearchHooks: Yahoo! Toolbar: {ef99bd32-c1fb-11d2-892f-0090271d4f88} -
BHO: Adobe PDF Reader Link Helper: {06849e9f-c8d7-4d59-b87d-784b7d6be0b3} - c:\program files\common files\adobe\acrobat\activex\AcroIEHelper.dll
BHO: Comcast Toolbar: {4e7bd74f-2b8d-469e-93be-be2df4d9ae29} - c:\progra~1\comcas~1\COMCAS~1.DLL
BHO: WhiteSmoke Toolbar: {52794457-af6c-4c50-9def-f2e24f4c8889} - c:\program files\whitesmoketoolbar\whitesmoketoolbarX.dll
BHO: SSVHelper Class: {761497bb-d6f0-462c-b6eb-d4daf1d92d43} - c:\program files\java\jre1.6.0_05\bin\ssv.dll
BHO: scriptproxy: {7db2d5a0-7241-4e79-b68d-6309f01c5231} - c:\program files\mcafee\virusscan\scriptsn.dll
TB: Acer eDataSecurity Management: {5cbe3b7c-1e47-477e-a7dd-396db0476e29} - c:\windows\system32\eDStoolbar.dll
TB: Comcast Toolbar: {4e7bd74f-2b8d-469e-93be-be2df4d9ae29} - c:\progra~1\comcas~1\COMCAS~1.DLL
TB: WhiteSmoke Toolbar: {52794457-af6c-4c50-9def-f2e24f4c8889} - c:\program files\whitesmoketoolbar\whitesmoketoolbarX.dll
TB: Yahoo! Toolbar: {ef99bd32-c1fb-11d2-892f-0090271d4f88} -
uRun: [MSMSGS] "c:\program files\messenger\msmsgs.exe" /background
uRun: [ctfmon.exe] c:\windows\system32\ctfmon.exe
mRun: [LaunchApp] Alaunch
mRun: [High Definition Audio Property Page Shortcut] HDAShCut.exe
mRun: [ntiMUI] c:\program files\newtech infosystems\nti cd & dvd-maker 7\ntiMUI.exe
mRun: [<NO NAME>]
mRun: [RemoteControl] "c:\program files\cyberlink\powerdvd\PDVDServ.exe"
mRun: [IMJPMIG8.1] "c:\windows\ime\imjp8_1\IMJPMIG.EXE" /Spoil /RemAdvDef /Migration32
mRun: [MSPY2002] c:\windows\system32\ime\pintlgnt\ImScInst.exe /SYNC
mRun: [PHIME2002ASync] c:\windows\system32\ime\tintlgnt\TINTSETP.EXE /SYNC
mRun: [PHIME2002A] c:\windows\system32\ime\tintlgnt\TINTSETP.EXE /IMEName
mRun: [igfxtray] c:\windows\system32\igfxtray.exe
mRun: [igfxhkcmd] c:\windows\system32\hkcmd.exe
mRun: [igfxpers] c:\windows\system32\igfxpers.exe
mRun: [SkyTel] SkyTel.EXE
mRun: [SunJavaUpdateSched] "c:\program files\java\jre1.6.0_05\bin\jusched.exe"
mRun: [eDataSecurity Loader] c:\acer\empowering technology\edatasecurity\eDSloader.exe 0
mRun: [RTHDCPL] RTHDCPL.EXE
mRun: [Alcmtr] ALCMTR.EXE
mRun: [eRecoveryService] c:\acer\empowering technology\erecovery\eRAgent.exe
mRun: [ATICCC] "c:\program files\ati technologies\ati.ace\CLIStart.exe"
mRun: [HPWUTOOLBOX] c:\program files\hp\hp officejet pro k550 series\toolbox\HPWUTBX.exe "-i"
mRun: [Adobe Reader Speed Launcher] "c:\program files\adobe\reader 8.0\reader\Reader_sl.exe"
mRun: [itype] "c:\program files\microsoft intellitype pro\itype.exe"
mRun: [IntelliPoint] "c:\program files\microsoft intellipoint\ipoint.exe"
mRun: [mcagent_exe] "c:\program files\mcafee.com\agent\mcagent.exe" /runkey
IE: {e2e2dd38-d088-4134-82b7-f2ba38496583} - %windir%\Network Diagnostic\xpnetdiag.exe
IE: {FB5F1910-F110-11d2-BB9E-00C04F795683} - c:\program files\messenger\msmsgs.exe
IE: {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - {CAFEEFAC-0016-0000-0005-ABCDEFFEDCBC} - c:\program files\java\jre1.6.0_05\bin\ssv.dll
DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} - hxxp://update.microsoft.com/windowsupdate/v6/V5Controls/en/x86/client/wuweb_site.cab?1166462899750
DPF: {8AD9C840-044E-11D1-B3E9-00805F499D93} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_05-windows-i586.cab
DPF: {CAFEEFAC-0015-0000-0006-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.5.0/jinstall-1_5_0_06-windows-i586.cab
DPF: {CAFEEFAC-0015-0000-0009-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.5.0/jinstall-1_5_0_09-windows-i586.cab
DPF: {CAFEEFAC-0015-0000-0010-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.5.0/jinstall-1_5_0_10-windows-i586.cab
DPF: {CAFEEFAC-0015-0000-0011-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.5.0/jinstall-1_5_0_11-windows-i586.cab
DPF: {CAFEEFAC-0016-0000-0001-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_01-windows-i586.cab
DPF: {CAFEEFAC-0016-0000-0002-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_02-windows-i586.cab
DPF: {CAFEEFAC-0016-0000-0003-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_03-windows-i586.cab
DPF: {CAFEEFAC-0016-0000-0005-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_05-windows-i586.cab
DPF: {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_05-windows-i586.cab
DPF: {D27CDB6E-AE6D-11CF-96B8-444553540000} - hxxp://fpdownload2.macromedia.com/get/shockwave/cabs/flash/swflash.cab
Notify: AtiExtEvent - Ati2evxx.dll
Notify: igfxcui - igfxdev.dll
SSODL: WPDShServiceObj - {AAA288BA-9A4C-45B0-95D7-94D524869DB5} - c:\windows\system32\WPDShServiceObj.dll
============= SERVICES / DRIVERS ===============
R? eLock2BurnerLockDriver;eLock2BurnerLockDriver
R? eLock2FSCTLDriver;eLock2FSCTLDriver
R? mferkdk;McAfee Inc. mferkdk
R? PortRW;PortRW
S? McProxy;McAfee Proxy Service
S? McShield;McAfee Real-time Scanner
S? McSysmon;McAfee SystemGuards
S? mfeavfk;McAfee Inc. mfeavfk
S? mfebopk;McAfee Inc. mfebopk
S? mfehidk;McAfee Inc. mfehidk
S? mfesmfk;McAfee Inc. mfesmfk
=============== Created Last 30 ================
2010-12-13 11:09:18 -------- d-----w- c:\docume~1\raymon~1\applic~1\whitesmoketoolbar
2010-12-13 06:47:46 -------- d-----w- c:\program files\whitesmoketoolbar
2010-12-13 06:47:33 -------- d-----w- c:\program files\WhiteSmoke Translator
2010-12-13 06:47:17 -------- d-----w- c:\windows\system32\%APPDATA%
2010-12-13 06:47:04 53248 ----a-w- c:\windows\system32\6to4v32.dll
==================== Find3M ====================
=================== ROOTKIT ====================
Stealth MBR rootkit/Mebroot/Sinowal/TDL4 detector 0.4.2 by Gmer, http://www.gmer.net
Windows 5.1.2600
CreateFile("\\.\PHYSICALDRIVE0"): The process cannot access the file because it is being used by another process.
device: opened successfully
user: error reading MBR
Disk trace:
called modules: ntkrnlpa.exe CLASSPNP.SYS disk.sys ACPI.sys hal.dll >>UNKNOWN [0x8A5E6735]<<
_asm { PUSH EBP; MOV EBP, ESP; PUSH ECX; MOV EAX, [EBP+0x8]; CMP EAX, [0x8a5ec990]; MOV EAX, [0x8a5eca0c]; PUSH EBX; PUSH ESI; MOV ESI, [EBP+0xc]; MOV EBX, [ESI+0x60]; PUSH EDI; JNZ 0x20; MOV [EBP+0x8], EAX; }
1 ntkrnlpa!IofCallDriver[0x804EEF9C] -> \Device\Harddisk0\DR0[0x8A649AB8]
3 CLASSPNP[0xBA8E905B] -> ntkrnlpa!IofCallDriver[0x804EEF9C] -> \Device\0000006a[0x8A630598]
5 ACPI[0xBA77F620] -> ntkrnlpa!IofCallDriver[0x804EEF9C] -> [0x8A66A940]
\Driver\atapi[0x8A657A08] -> IRP_MJ_CREATE -> 0x8A5E6735
kernel: MBR read successfully
_asm { XOR AX, AX; MOV SS, AX; MOV SP, 0x7c00; STI ; PUSH AX; POP ES; PUSH AX; POP DS; CLD ; MOV SI, 0x7c1b; MOV DI, 0x61b; PUSH AX; PUSH DI; MOV CX, 0x1e5; REP MOVSB ; RETF ; MOV DI, 0x5; XOR AX, AX; MOV DL, 0x80; INT 0x13; JAE 0x2d; DEC DI; }
detected disk devices:
detected hooks:
\Driver\atapi DriverStartIo -> 0x8A5E657B
user != kernel MBR !!!
Warning: possible TDL4 rootkit infection !
TDL4 rootkit infection detected ! Use: "mbr.exe -f" to fix.
============= FINISH: 23:49:20.75 ===============
==== Installed Programs ======================
Acer eDataSecurity Management
Adobe Flash Player 10 ActiveX
Adobe Reader 8.1.0
ATI - Software Uninstall Utility
ATI Catalyst Control Center
ATI Display Driver
ATI HYDRAVISION
ATI Parental Control & Encoder
ATI Problem Report Wizard
AVIVO Codecs
Comcast Toolbar
ERUNT 1.1j
eSignal
Fibonacci Trader 4
Fibonacci/Galactic Trader 4
High Definition Audio Driver Package - KB888111
Hotfix for Windows XP (KB893357)
Hotfix for Windows XP (KB896256)
Hotfix for Windows XP (KB896344)
Hotfix for Windows XP (KB906569)
Hotfix for Windows XP (KB914440)
Hotfix for Windows XP (KB915865)
Hotfix for Windows XP (KB926239)
Hotfix for Windows XP (KB928388)
Hotfix for Windows XP (KB929120)
HP Officejet Pro K550 Series
Intel(R) Graphics Media Accelerator Driver
J2SE Runtime Environment 5.0 Update 10
J2SE Runtime Environment 5.0 Update 11
J2SE Runtime Environment 5.0 Update 6
J2SE Runtime Environment 5.0 Update 9
Java(TM) 6 Update 2
Java(TM) 6 Update 3
Java(TM) 6 Update 5
Java(TM) SE Runtime Environment 6 Update 1
Malwarebytes' Anti-Malware
McAfee SecurityCenter
Microsoft .NET Framework 1.1
Microsoft .NET Framework 1.1 Hotfix (KB886903)
Microsoft .NET Framework 2.0
Microsoft Base Smart Card Cryptographic Service Provider Package
Microsoft Compression Client Pack 1.0 for Windows XP
Microsoft IntelliPoint 6.1
Microsoft IntelliType Pro 6.1
Microsoft Internationalized Domain Names Mitigation APIs
Microsoft National Language Support Downlevel APIs
Microsoft User-Mode Driver Framework Feature Pack 1.0
Microsoft Visual C++ 2005 Redistributable
Misc
NTI Backup NOW! 4
NTI CD & DVD-Maker
OCA Client history tool install
PartitionMagic
PowerDVD
PowerQuest PartitionMagic 8.0
Realtek High Definition Audio Driver
Security Update for Microsoft .NET Framework 2.0 (KB917283)
Security Update for Microsoft .NET Framework 2.0 (KB922770)
Security Update for Step By Step Interactive Training (KB898458)
Security Update for Windows Media Player (KB911564)
Security Update for Windows Media Player 6.4 (KB925398)
Security Update for Windows Media Player 9 (KB917734)
Security Update for Windows XP (KB883939)
Security Update for Windows XP (KB890046)
Security Update for Windows XP (KB893756)
Security Update for Windows XP (KB896358)
Security Update for Windows XP (KB896422)
Security Update for Windows XP (KB896423)
Security Update for Windows XP (KB896424)
Security Update for Windows XP (KB896428)
Security Update for Windows XP (KB899587)
Security Update for Windows XP (KB899588)
Security Update for Windows XP (KB899589)
Security Update for Windows XP (KB899591)
Security Update for Windows XP (KB900725)
Security Update for Windows XP (KB901017)
Security Update for Windows XP (KB901190)
Security Update for Windows XP (KB901214)
Security Update for Windows XP (KB902400)
Security Update for Windows XP (KB903235)
Security Update for Windows XP (KB904706)
Security Update for Windows XP (KB905414)
Security Update for Windows XP (KB905749)
Security Update for Windows XP (KB905915)
Security Update for Windows XP (KB908519)
Security Update for Windows XP (KB911562)
Security Update for Windows XP (KB911927)
Security Update for Windows XP (KB912919)
Security Update for Windows XP (KB913446)
Security Update for Windows XP (KB913580)
Security Update for Windows XP (KB914388)
Security Update for Windows XP (KB914389)
Security Update for Windows XP (KB917344)
Security Update for Windows XP (KB917422)
Security Update for Windows XP (KB917953)
Security Update for Windows XP (KB918439)
Security Update for Windows XP (KB919007)
Security Update for Windows XP (KB920213)
Security Update for Windows XP (KB920670)
Security Update for Windows XP (KB920683)
Security Update for Windows XP (KB920685)
Security Update for Windows XP (KB921398)
Security Update for Windows XP (KB922616)
Security Update for Windows XP (KB922819)
Security Update for Windows XP (KB923191)
Security Update for Windows XP (KB923414)
Security Update for Windows XP (KB923689)
Security Update for Windows XP (KB923694)
Security Update for Windows XP (KB923789)
Security Update for Windows XP (KB923980)
Security Update for Windows XP (KB924191)
Security Update for Windows XP (KB924270)
Security Update for Windows XP (KB924496)
Security Update for Windows XP (KB925454)
Security Update for Windows XP (KB925486)
Security Update for Windows XP (KB926255)
Sentinel System Driver
Spybot - Search & Destroy
Toolbox
Trading Rooms Technologies, Inc TradingRooms Application
UGuide
Update for Windows XP (KB894391)
Update for Windows XP (KB896727)
Update for Windows XP (KB898461)
Update for Windows XP (KB900485)
Update for Windows XP (KB904942)
Update for Windows XP (KB908531)
Update for Windows XP (KB910437)
Update for Windows XP (KB911280)
Update for Windows XP (KB912945)
Update for Windows XP (KB916595)
Update for Windows XP (KB920342)
Update for Windows XP (KB920872)
Update for Windows XP (KB922582)
Update for Windows XP (KB925876)
WebFldrs XP
Whitesmoke Translator
Windows Genuine Advantage Validation Tool (KB892130)
Windows Installer 3.1 (KB893803)
Windows Internet Explorer 7
Windows Media Format 11 runtime
Windows Media Format SDK Hotfix - KB891122
Windows Media Player 11
Windows Rights Management Client Backwards Compatibility SP2
Windows Rights Management Client with Service Pack 2
Windows XP Hotfix - KB867282
Windows XP Hotfix - KB873333
Windows XP Hotfix - KB873339
Windows XP Hotfix - KB885250
Windows XP Hotfix - KB885835
Windows XP Hotfix - KB885836
Windows XP Hotfix - KB886185
Windows XP Hotfix - KB887472
Windows XP Hotfix - KB888113
Windows XP Hotfix - KB888302
Windows XP Hotfix - KB890047
Windows XP Hotfix - KB890175
Windows XP Hotfix - KB890859
Windows XP Hotfix - KB890923
Windows XP Hotfix - KB891781
Windows XP Hotfix - KB893086
==== End Of File ===========================
-

Hi,
Before we proceed, you had Malwarebytes set to TAKE NO ACTION, rerun Malwarebytes and this time make sure you select FIX CHECKED. Then post the new Malwarebytes log. You can attach it, thats fine.
Your computer is also infected with a rootkit
- Download TDSSKiller and save it to your Desktop.
- Extract the file and run it.
- Once completed it will create a log in your C:\ drive called TDSSKiller_* (* denotes version & date)
- Please post the content of the TDSSKiller log
-

The Malwarebyte fixes were run on 800+ problems.
White Smoke icons are still on the desktop.
That could be because I didn't reboot the computer as Malware asked.
I am concerned about whether the computer will boot back up in normal mode. Although it may bootup in Safe Mode, I don't know what the ability is to troubleshoot from Safe Mode.
I re-ran Malwarebytes and no problems were found (attached log).
However, since the desktop will not connect to the internet, update of the database wasn't possible. Last update was Dec 13, 2010
If you want me to reboot, let me know.
I understand the risk.
Tddsskiller is being run and a log will be posted shortly.
Here is the Malwarebytes log
Malwarebytes' Anti-Malware 1.50
www.malwarebytes.org
Database version: 5305
Windows 5.1.2600 Service Pack 2
Internet Explorer 7.0.5730.11
12/19/2010 7:51:37 AM
mbam-log-2010-12-19 (07-51-37).txt
Scan type: Full scan (C:\|D:\|F:\|)
Objects scanned: 298240
Time elapsed: 45 minute(s), 59 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
-

TDSSKiller found 1 problem and it was corrected.
The computer hasn't been rebooted yet to clean up everything.
I will await for you call on that one.
Also, the desktop is stil unable to connect to the internet (awaiting a reboot?), even thought Network Connections list the Local Area Connection and Internet Connection as 'Connected'.
Here is the TDSSkiller log.
2010/12/19 08:18:48.0671 TDSS rootkit removing tool 2.4.12.0 Dec 16 2010 09:46:46
2010/12/19 08:18:48.0671 ================================================================================
2010/12/19 08:18:48.0671 SystemInfo:
2010/12/19 08:18:48.0671
2010/12/19 08:18:48.0671 OS Version: 5.1.2600 ServicePack: 2.0
2010/12/19 08:18:48.0671 Product type: Workstation
2010/12/19 08:18:48.0671 ComputerName: RAYMOND-DESKTOP
2010/12/19 08:18:48.0671 UserName: Raymond Green
2010/12/19 08:18:48.0671 Windows directory: C:\WINDOWS
2010/12/19 08:18:48.0671 System windows directory: C:\WINDOWS
2010/12/19 08:18:48.0671 Processor architecture: Intel x86
2010/12/19 08:18:48.0671 Number of processors: 2
2010/12/19 08:18:48.0671 Page size: 0x1000
2010/12/19 08:18:48.0671 Boot type: Normal boot
2010/12/19 08:18:48.0671 ================================================================================
2010/12/19 08:18:53.0531 Initialize success
2010/12/19 08:18:58.0375 ================================================================================
2010/12/19 08:18:58.0375 Scan started
2010/12/19 08:18:58.0375 Mode: Manual;
2010/12/19 08:18:58.0375 ================================================================================
2010/12/19 08:18:59.0093 ACPI (a10c7534f7223f4a73a948967d00e69b) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2010/12/19 08:18:59.0125 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2010/12/19 08:18:59.0234 aec (1ee7b434ba961ef845de136224c30fec) C:\WINDOWS\system32\drivers\aec.sys
2010/12/19 08:18:59.0265 AFD (5ac495f4cb807b2b98ad2ad591e6d92e) C:\WINDOWS\System32\drivers\afd.sys
2010/12/19 08:18:59.0500 AsyncMac (02000abf34af4c218c35d257024807d6) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2010/12/19 08:18:59.0531 atapi (cdfe4411a69c224bd1d11b2da92dac51) C:\WINDOWS\system32\DRIVERS\atapi.sys
2010/12/19 08:18:59.0656 ati2mtag (86a7a22f3670465ef575614e001159c0) C:\WINDOWS\system32\DRIVERS\ati2mtag.sys
2010/12/19 08:18:59.0796 Atmarpc (ec88da854ab7d7752ec8be11a741bb7f) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2010/12/19 08:18:59.0828 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2010/12/19 08:18:59.0859 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
2010/12/19 08:18:59.0890 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2010/12/19 08:18:59.0953 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2010/12/19 08:18:59.0984 Cdfs (cd7d5152df32b47f4e36f710b35aae02) C:\WINDOWS\system32\drivers\Cdfs.sys
2010/12/19 08:19:00.0031 Cdrom (af9c19b3100fe010496b1a27181fbf72) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2010/12/19 08:19:00.0281 Disk (00ca44e4534865f8a3b64f7c0984bff0) C:\WINDOWS\system32\DRIVERS\disk.sys
2010/12/19 08:19:00.0359 dmboot (c0fbb516e06e243f0cf31f597e7ebf7d) C:\WINDOWS\system32\drivers\dmboot.sys
2010/12/19 08:19:00.0406 dmio (f5e7b358a732d09f4bcf2824b88b9e28) C:\WINDOWS\system32\drivers\dmio.sys
2010/12/19 08:19:00.0453 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2010/12/19 08:19:00.0500 DMusic (a6f881284ac1150e37d9ae47ff601267) C:\WINDOWS\system32\drivers\DMusic.sys
2010/12/19 08:19:00.0578 drmkaud (1ed4dbbae9f5d558dbba4cc450e3eb2e) C:\WINDOWS\system32\drivers\drmkaud.sys
2010/12/19 08:19:00.0656 Fastfat (3117f595e9615e04f05a54fc15a03b20) C:\WINDOWS\system32\drivers\Fastfat.sys
2010/12/19 08:19:00.0734 Fdc (ced2e8396a8838e59d8fd529c680e02c) C:\WINDOWS\system32\DRIVERS\fdc.sys
2010/12/19 08:19:00.0750 Fips (e153ab8a11de5452bcf5ac7652dbf3ed) C:\WINDOWS\system32\drivers\Fips.sys
2010/12/19 08:19:00.0796 Flpydisk (0dd1de43115b93f4d85e889d7a86f548) C:\WINDOWS\system32\DRIVERS\flpydisk.sys
2010/12/19 08:19:00.0875 FltMgr (3d234fb6d6ee875eb009864a299bea29) C:\WINDOWS\system32\DRIVERS\fltMgr.sys
2010/12/19 08:19:01.0000 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2010/12/19 08:19:01.0031 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2010/12/19 08:19:01.0046 Gpc (c0f1d4a21de5a415df8170616703debf) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2010/12/19 08:19:01.0125 HdAudAddService (2a013e7530beab6e569faa83f517e836) C:\WINDOWS\system32\drivers\HdAudio.sys
2010/12/19 08:19:01.0171 HDAudBus (3fcc124b6e08ee0e9351f717dd136939) C:\WINDOWS\system32\DRIVERS\HDAudBus.sys
2010/12/19 08:19:01.0218 hidusb (1de6783b918f540149aa69943bdfeba8) C:\WINDOWS\system32\DRIVERS\hidusb.sys
2010/12/19 08:19:01.0312 HTTP (cb77bb47e67e84deb17ba29632501730) C:\WINDOWS\system32\Drivers\HTTP.sys
2010/12/19 08:19:01.0500 i8042prt (5502b58eef7486ee6f93f3f164dcb808) C:\WINDOWS\system32\DRIVERS\i8042prt.sys
2010/12/19 08:19:01.0578 ialm (9a883c3c4d91292c0d09de7c728e781c) C:\WINDOWS\system32\DRIVERS\ialmnt5.sys
2010/12/19 08:19:01.0640 Imapi (f8aa320c6a0409c0380e5d8a99d76ec6) C:\WINDOWS\system32\DRIVERS\imapi.sys
2010/12/19 08:19:01.0796 int15.sys (4d8d5b1c895ea0f2a721b98a7ce198f1) C:\Acer\Empowering Technology\eRecovery\int15.sys
2010/12/19 08:19:02.0031 IntcAzAudAddService (284bcb80391783d328a8d8163e97fd58) C:\WINDOWS\system32\drivers\RtkHDAud.sys
2010/12/19 08:19:02.0390 intelppm (279fb78702454dff2bb445f238c048d2) C:\WINDOWS\system32\DRIVERS\intelppm.sys
2010/12/19 08:19:02.0421 Ip6Fw (4448006b6bc60e6c027932cfc38d6855) C:\WINDOWS\system32\DRIVERS\Ip6Fw.sys
2010/12/19 08:19:02.0437 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2010/12/19 08:19:02.0468 IpInIp (e1ec7f5da720b640cd8fb8424f1b14bb) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2010/12/19 08:19:02.0515 IpNat (e2168cbc7098ffe963c6f23f472a3593) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2010/12/19 08:19:02.0546 IPSec (64537aa5c003a6afeee1df819062d0d1) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2010/12/19 08:19:02.0625 IRENUM (50708daa1b1cbb7d6ac1cf8f56a24410) C:\WINDOWS\system32\DRIVERS\irenum.sys
2010/12/19 08:19:02.0671 isapnp (e504f706ccb699c2596e9a3da1596e87) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2010/12/19 08:19:02.0718 Kbdclass (ebdee8a2ee5393890a1acee971c4c246) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2010/12/19 08:19:02.0750 kbdhid (e182fa8e49e8ee41b4adc53093f3c7e6) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
2010/12/19 08:19:02.0796 kmixer (ba5deda4d934e6288c2f66caf58d2562) C:\WINDOWS\system32\drivers\kmixer.sys
2010/12/19 08:19:02.0828 KSecDD (eb7ffe87fd367ea8fca0506f74a87fbb) C:\WINDOWS\system32\drivers\KSecDD.sys
2010/12/19 08:19:02.0953 mfeavfk (bafdd5e28baea99d7f4772af2f5ec7ee) C:\WINDOWS\system32\drivers\mfeavfk.sys
2010/12/19 08:19:03.0015 mfebopk (1d003e3056a43d881597d6763e83b943) C:\WINDOWS\system32\drivers\mfebopk.sys
2010/12/19 08:19:03.0171 mfehidk (3f138a1c8a0659f329f242d1e389b2cf) C:\WINDOWS\system32\drivers\mfehidk.sys
2010/12/19 08:19:03.0265 mferkdk (41fe2f288e05a6c8ab85dd56770ffbad) C:\WINDOWS\system32\drivers\mferkdk.sys
2010/12/19 08:19:03.0312 mfesmfk (096b52ea918aa909ba5903d79e129005) C:\WINDOWS\system32\drivers\mfesmfk.sys
2010/12/19 08:19:03.0437 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2010/12/19 08:19:03.0500 Modem (6fc6f9d7acc36dca9b914565a3aeda05) C:\WINDOWS\system32\drivers\Modem.sys
2010/12/19 08:19:03.0546 MODEMCSA (1992e0d143b09653ab0f9c5e04b0fd65) C:\WINDOWS\system32\drivers\MODEMCSA.sys
2010/12/19 08:19:03.0640 Mouclass (34e1f0031153e491910e12551400192c) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2010/12/19 08:19:03.0687 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
2010/12/19 08:19:03.0734 MountMgr (65653f3b4477f3c63e68a9659f85ee2e) C:\WINDOWS\system32\drivers\MountMgr.sys
2010/12/19 08:19:03.0765 MPFP (136157e79849b9e5316ba4008d6075a8) C:\WINDOWS\system32\Drivers\Mpfp.sys
2010/12/19 08:19:03.0812 MRxDAV (46edcc8f2db2f322c24f48785cb46366) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2010/12/19 08:19:03.0859 MRxSmb (025af03ce51645c62f3b6907a7e2be5e) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2010/12/19 08:19:03.0906 Msfs (561b3a4333ca2dbdba28b5b956822519) C:\WINDOWS\system32\drivers\Msfs.sys
2010/12/19 08:19:03.0953 MSKSSRV (ae431a8dd3c1d0d0610cdbac16057ad0) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2010/12/19 08:19:04.0000 MSPCLOCK (13e75fef9dfeb08eeded9d0246e1f448) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2010/12/19 08:19:04.0031 MSPQM (1988a33ff19242576c3d0ef9ce785da7) C:\WINDOWS\system32\drivers\MSPQM.sys
2010/12/19 08:19:04.0046 mssmbios (469541f8bfd2b32659d5d463a6714bce) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2010/12/19 08:19:04.0078 Mup (82035e0f41c2dd05ae41d27fe6cf7de1) C:\WINDOWS\system32\drivers\Mup.sys
2010/12/19 08:19:04.0109 NDIS (558635d3af1c7546d26067d5d9b6959e) C:\WINDOWS\system32\drivers\NDIS.sys
2010/12/19 08:19:04.0187 NdisTapi (08d43bbdacdf23f34d79e44ed35c1b4c) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2010/12/19 08:19:04.0218 Ndisuio (8d3ce6b579cde8d37acc690b67dc2106) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2010/12/19 08:19:04.0250 NdisWan (0b90e255a9490166ab368cd55a529893) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2010/12/19 08:19:04.0296 NDProxy (59fc3fb44d2669bc144fd87826bb571f) C:\WINDOWS\system32\drivers\NDProxy.sys
2010/12/19 08:19:04.0328 NetBIOS (3a2aca8fc1d7786902ca434998d7ceb4) C:\WINDOWS\system32\DRIVERS\netbios.sys
2010/12/19 08:19:04.0375 NetBT (0c80e410cd2f47134407ee7dd19cc86b) C:\WINDOWS\system32\DRIVERS\netbt.sys
2010/12/19 08:19:04.0437 Npfs (4f601bcb8f64ea3ac0994f98fed03f8e) C:\WINDOWS\system32\drivers\Npfs.sys
2010/12/19 08:19:04.0500 Ntfs (b78be402c3f63dd55521f73876951cdd) C:\WINDOWS\system32\drivers\Ntfs.sys
2010/12/19 08:19:04.0531 NTIDrvr (7f1c1f78d709c4a54cbb46ede7e0b48d) C:\WINDOWS\system32\DRIVERS\NTIDrvr.sys
2010/12/19 08:19:04.0625 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2010/12/19 08:19:04.0656 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2010/12/19 08:19:04.0687 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2010/12/19 08:19:04.0734 Parport (29744eb4ce659dfe3b4122deb45bc478) C:\WINDOWS\system32\DRIVERS\parport.sys
2010/12/19 08:19:04.0781 PartMgr (3334430c29dc338092f79c38ef7b4cd0) C:\WINDOWS\system32\drivers\PartMgr.sys
2010/12/19 08:19:04.0828 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2010/12/19 08:19:04.0859 PCI (8086d9979234b603ad5bc2f5d890b234) C:\WINDOWS\system32\DRIVERS\pci.sys
2010/12/19 08:19:04.0906 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2010/12/19 08:19:04.0953 Pcmcia (82a087207decec8456fbe8537947d579) C:\WINDOWS\system32\drivers\Pcmcia.sys
2010/12/19 08:19:05.0203 Point32 (dcdf0421a1c14f2923e298a30fd7636d) C:\WINDOWS\system32\DRIVERS\point32.sys
2010/12/19 08:19:05.0250 PortRW (a7e67865db59e54801122077df8ade36) C:\WINDOWS\system32\Drivers\PortRW.sys
2010/12/19 08:19:05.0343 PptpMiniport (1c5cc65aac0783c344f16353e60b72ac) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2010/12/19 08:19:05.0390 PQNTDrv (b26019a686d36e22f954e67c8fec4297) C:\WINDOWS\system32\drivers\PQNTDrv.sys
2010/12/19 08:19:05.0500 PSched (48671f327553dcf1d27f6197f622a668) C:\WINDOWS\system32\DRIVERS\psched.sys
2010/12/19 08:19:05.0578 psdfilter (00b670d8a36c7134cfc66b446a18cc92) C:\WINDOWS\system32\Drivers\psdfilter.sys
2010/12/19 08:19:05.0593 psdvdisk (e9a60343cb7c39090638b1dd574f26eb) C:\WINDOWS\system32\Drivers\psdvdisk.sys
2010/12/19 08:19:05.0625 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2010/12/19 08:19:05.0812 qsnpyk (e6d35f3aa51a65eb35c1f2340154a25e) C:\WINDOWS\system32\drivers\lcxse.sys
2010/12/19 08:19:05.0859 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2010/12/19 08:19:05.0906 Rasl2tp (98faeb4a4dcf812ba1c6fca4aa3e115c) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2010/12/19 08:19:05.0921 RasPppoe (7306eeed8895454cbed4669be9f79faa) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2010/12/19 08:19:05.0953 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2010/12/19 08:19:06.0000 Rdbss (03b965b1ca47f6ef60eb5e51cb50e0af) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2010/12/19 08:19:06.0046 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2010/12/19 08:19:06.0093 rdpdr (a2cae2c60bc37e0751ef9dda7ceaf4ad) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
2010/12/19 08:19:06.0156 RDPWD (b54cd38a9ebfbf2b3561426e3fe26f62) C:\WINDOWS\system32\drivers\RDPWD.sys
2010/12/19 08:19:06.0218 redbook (b31b4588e4086d8d84adbf9845c2402b) C:\WINDOWS\system32\DRIVERS\redbook.sys
2010/12/19 08:19:06.0343 Secdrv (d26e26ea516450af9d072635c60387f4) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2010/12/19 08:19:06.0421 Sentinel (8627c992b8a80504fc477b2e8ff8ec4f) C:\WINDOWS\System32\Drivers\SENTINEL.SYS
2010/12/19 08:19:06.0468 serenum (a2d868aeeff612e70e213c451a70cafb) C:\WINDOWS\system32\DRIVERS\serenum.sys
2010/12/19 08:19:06.0500 Serial (cd9404d115a00d249f70a371b46d5a26) C:\WINDOWS\system32\DRIVERS\serial.sys
2010/12/19 08:19:06.0531 Sfloppy (0d13b6df6e9e101013a7afb0ce629fe0) C:\WINDOWS\system32\drivers\Sfloppy.sys
2010/12/19 08:19:06.0609 SNTNLUSB (87f799c486302aceff098e067d481d9c) C:\WINDOWS\system32\DRIVERS\SNTNLUSB.SYS
2010/12/19 08:19:06.0781 splitter (0ce218578fff5f4f7e4201539c45c78f) C:\WINDOWS\system32\drivers\splitter.sys
2010/12/19 08:19:06.0812 sr (e41b6d037d6cd08461470af04500dc24) C:\WINDOWS\system32\DRIVERS\sr.sys
2010/12/19 08:19:06.0875 Srv (ea554a3ffc3f536fe8320eb38f5e4843) C:\WINDOWS\system32\DRIVERS\srv.sys
2010/12/19 08:19:06.0953 swenum (03c1bae4766e2450219d20b993d6e046) C:\WINDOWS\system32\DRIVERS\swenum.sys
2010/12/19 08:19:07.0000 swmidi (94abc808fc4b6d7d2bbf42b85e25bb4d) C:\WINDOWS\system32\drivers\swmidi.sys
2010/12/19 08:19:07.0156 sysaudio (650ad082d46bac0e64c9c0e0928492fd) C:\WINDOWS\system32\drivers\sysaudio.sys
2010/12/19 08:19:07.0218 Tcpip (1dbf125862891817f374f407626967f4) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2010/12/19 08:19:07.0265 TDPIPE (38d437cf2d98965f239b0abcd66dcb0f) C:\WINDOWS\system32\drivers\TDPIPE.sys
2010/12/19 08:19:07.0312 TDTCP (ed0580af02502d00ad8c4c066b156be9) C:\WINDOWS\system32\drivers\TDTCP.sys
2010/12/19 08:19:07.0359 TermDD (a540a99c281d933f3d69d55e48727f47) C:\WINDOWS\system32\DRIVERS\termdd.sys
2010/12/19 08:19:07.0468 UBHelper (e0c67be430c6de490d6ccaecfa071f9e) C:\WINDOWS\system32\drivers\UBHelper.sys
2010/12/19 08:19:07.0546 Udfs (12f70256f140cd7d52c58c7048fde657) C:\WINDOWS\system32\drivers\Udfs.sys
2010/12/19 08:19:07.0625 Update (aff2e5045961bbc0a602bb6f95eb1345) C:\WINDOWS\system32\DRIVERS\update.sys
2010/12/19 08:19:07.0718 usbccgp (bffd9f120cc63bcbaa3d840f3eef9f79) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2010/12/19 08:19:07.0765 usbehci (15e993ba2f6946b2bfbbfcd30398621e) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2010/12/19 08:19:07.0796 usbhub (c72f40947f92cea56a8fb532edf025f1) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2010/12/19 08:19:07.0828 usbprint (a42369b7cd8886cd7c70f33da6fcbcf5) C:\WINDOWS\system32\DRIVERS\usbprint.sys
2010/12/19 08:19:07.0875 USBSTOR (6cd7b22193718f1d17a47a1cd6d37e75) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2010/12/19 08:19:07.0890 usbuhci (f8fd1400092e23c8f2f31406ef06167b) C:\WINDOWS\system32\DRIVERS\usbuhci.sys
2010/12/19 08:19:07.0921 VgaSave (8a60edd72b4ea5aea8202daf0e427925) C:\WINDOWS\System32\drivers\vga.sys
2010/12/19 08:19:07.0968 VolSnap (ee4660083deba849ff6c485d944b379b) C:\WINDOWS\system32\drivers\VolSnap.sys
2010/12/19 08:19:08.0078 Wanarp (984ef0b9788abf89974cfed4bfbaacbc) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2010/12/19 08:19:08.0156 wdmaud (efd235ca22b57c81118c1aeb4798f1c1) C:\WINDOWS\system32\drivers\wdmaud.sys
2010/12/19 08:19:08.0328 WudfPf (f15feafffbb3644ccc80c5da584e6311) C:\WINDOWS\system32\DRIVERS\WudfPf.sys
2010/12/19 08:19:08.0390 WudfRd (28b524262bce6de1f7ef9f510ba3985b) C:\WINDOWS\system32\DRIVERS\wudfrd.sys
2010/12/19 08:19:08.0453 yukonwxp (ba6d2b32372a879aa817829c7cd2cb15) C:\WINDOWS\system32\DRIVERS\yk51x86.sys
2010/12/19 08:19:08.0703 \HardDisk1 - detected Rootkit.Win32.TDSS.tdl4 (0)
2010/12/19 08:19:08.0734 ================================================================================
2010/12/19 08:19:08.0734 Scan finished
2010/12/19 08:19:08.0734 ================================================================================
2010/12/19 08:19:08.0750 Detected object count: 1
2010/12/19 08:19:35.0203 \HardDisk1 - will be cured after reboot
2010/12/19 08:19:35.0203 Rootkit.Win32.TDSS.tdl4(\HardDisk1) - User select action: Cure
-

You will need to reboot for the TDSSkiller fix to take. What this rootkit has done was infected your Master Boot Record, thats most likely why you could not boot up
After you reboot than run this program.
Download ComboFix from one of these locations:
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools
- See this Link for programs that need to be disabled and instruction on how to disable them.
- Remember to re-enable them when we're done.
- Double click on ComboFix.exe & follow the prompts.
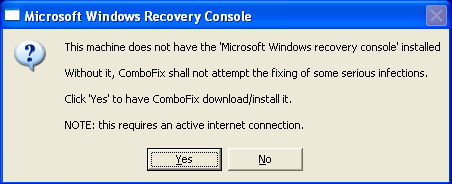
- As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
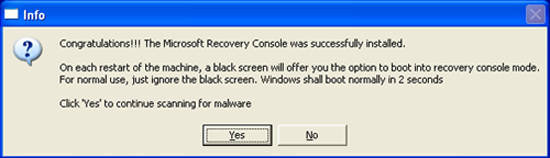
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
*If there is no internet connection when Combofix has completely finished then restart your computer to restore back the connections.
 Posting Permissions
Posting Permissions
- You may not post new threads
- You may not post replies
- You may not post attachments
- You may not edit your posts
-
Forum Rules