-
 Windows XP Recovery, No DDS!
Windows XP Recovery, No DDS!
This lame virus, Windows XP Recovery, appeared yesterday. I have booted up in Safe Mode with Networking, however I can not see all my programs and my desk top is black. I think this virus has been here for awhile as my computer has been very slow, Not Responding in certain programs. I have nothing further at this time and will stand by for further instructions.
Thanks, Tim
.
DDS (Ver_11-05-19.01) - NTFSx86 NETWORK
Internet Explorer: 8.0.6001.18702 BrowserJavaVersion: 1.6.0_23
Run by Tim at 11:31:50 on 2011-05-29
Microsoft Windows XP Home Edition 5.1.2600.3.1252.1.1033.18.254.22 [GMT -4:00]
.
AV: AntiVir Desktop *Disabled/Updated* {AD166499-45F9-482A-A743-FDD3350758C7}
FW: Outpost Security Suite *Disabled*
.
============== Running Processes ===============
.
C:\WINDOWS\system32\svchost -k DcomLaunch
svchost.exe
C:\WINDOWS\System32\svchost.exe -k netsvcs
svchost.exe
svchost.exe
C:\WINDOWS\Explorer.EXE
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Internet Explorer\iexplore.exe
C:\Program Files\Internet Explorer\iexplore.exe
C:\Documents and Settings\Tim\Desktop\dds.scr
C:\WINDOWS\system32\WSCRIPT.exe
.
============== Pseudo HJT Report ===============
.
uStart Page = hxxp://www.app.com/
mStart Page = hxxp://www.msn.com
uInternet Settings,ProxyOverride = localhost
mURLSearchHooks: H - No File
BHO: Adobe PDF Reader Link Helper: {06849e9f-c8d7-4d59-b87d-784b7d6be0b3} - c:\program files\common files\adobe\acrobat\activex\AcroIEHelper.dll
BHO: DriveLetterAccess: {5ca3d70e-1895-11cf-8e15-001234567890} - c:\windows\system32\dla\tfswshx.dll
BHO: Java(tm) Plug-In 2 SSV Helper: {dbc80044-a445-435b-bc74-9c25c1c588a9} - c:\program files\java\jre6\bin\jp2ssv.dll
BHO: JQSIEStartDetectorImpl Class: {e7e6f031-17ce-4c07-bc86-eabfe594f69c} - c:\program files\java\jre6\lib\deploy\jqs\ie\jqs_plugin.dll
TB: {2318C2B1-4965-11D4-9B18-009027A5CD4F} - No File
TB: {4982D40A-C53B-4615-B15B-B5B5E98D167C} - No File
TB: &Yahoo! Toolbar: {ef99bd32-c1fb-11d2-892f-0090271d4f88} -
TB: {A057A204-BACC-4D26-9990-79A187E2698E} - No File
uRun: [ctfmon.exe] c:\windows\system32\ctfmon.exe
uRun: [ISUSPM] "c:\program files\common files\installshield\updateservice\ISUSPM.exe" -scheduler
uRun: [LoBoUYvVYw] c:\documents and settings\all users\application data\LoBoUYvVYw.exe
mRun: [avgnt] "c:\program files\avira\antivir desktop\avgnt.exe" /min
mRun: [OutpostMonitor] "c:\progra~1\agnitum\outpos~1\op_mon.exe" /tray /noservice
mRun: [OutpostFeedBack] "c:\program files\agnitum\outpost security suite free\feedback.exe" /dump:os_startup
mRun: [QuickTime Task] "c:\program files\quicktime\qttask.exe" -atboottime
mRun: [Adobe Reader Speed Launcher] "c:\program files\adobe\reader 8.0\reader\Reader_sl.exe"
mRun: [Adobe ARM] "c:\program files\common files\adobe\arm\1.0\AdobeARM.exe"
mRun: [KernelFaultCheck] %systemroot%\system32\dumprep 0 -k
uPolicies-explorer: NoDesktop = 1 (0x1)
uPolicies-system: DisableTaskMgr = 1 (0x1)
mPolicies-system: DisableTaskMgr = 1 (0x1)
IE: {CD67F990-D8E9-11d2-98FE-00C0F0318AFE}
IE: {e2e2dd38-d088-4134-82b7-f2ba38496583} - %windir%\Network Diagnostic\xpnetdiag.exe
IE: {FB5F1910-F110-11d2-BB9E-00C04F795683} - c:\program files\messenger\msmsgs.exe
IE: {92780B25-18CC-41C8-B9BE-3C9C571A8263} - {FF059E31-CC5A-4E2E-BF3B-96E929D65503} - c:\progra~1\micros~4\office11\REFIEBAR.DLL
DPF: {01113300-3E00-11D2-8470-0060089874ED} - hxxps://activatemyfios.verizon.net/sdcCommon/download/FIOS/Verizon%20FiOS%20Installer.cab
DPF: {166B1BCA-3F9C-11CF-8075-444553540000} - hxxp://fpdownload.macromedia.com/get/shockwave/cabs/director/sw.cab
DPF: {6E32070A-766D-4EE6-879C-DC1FA91D2FC3} - hxxp://www.update.microsoft.com/microsoftupdate/v6/V5Controls/en/x86/client/muweb_site.cab?1254591051484
DPF: {6F750203-1362-4815-A476-88533DE61D0C} - hxxp://www.kodakgallery.com/downloads/BUM/BUM_WIN_IE_2/axofupld.cab
DPF: {7530BFB8-7293-4D34-9923-61A11451AFC5} - hxxp://download.eset.com/special/eos/OnlineScanner.cab
DPF: {8AD9C840-044E-11D1-B3E9-00805F499D93} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_23-windows-i586.cab
DPF: {9600F64D-755F-11D4-A47F-0001023E6D5A} - hxxp://web1.shutterfly.com/downloads/Uploader.cab
DPF: {BCBC9371-595D-11D4-A96D-00105A1CEF6C} - hxxp://onlinedesigner.hgtv.com/images/app/view22rte.cab
DPF: {CAFEEFAC-0016-0000-0023-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_23-windows-i586.cab
DPF: {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_23-windows-i586.cab
DPF: {D27CDB6E-AE6D-11CF-96B8-444553540000} - hxxp://fpdownload2.macromedia.com/get/shockwave/cabs/flash/swflash.cab
Notify: igfxcui - igfxdev.dll
AppInit_DLLs: c:\progra~1\agnitum\outpos~1\wl_hook.dll
SSODL: WPDShServiceObj - {AAA288BA-9A4C-45B0-95D7-94D524869DB5} - c:\windows\system32\WPDShServiceObj.dll
.
============= SERVICES / DRIVERS ===============
.
S1 avgio;avgio;c:\program files\avira\antivir desktop\avgio.sys [2011-1-3 11608]
S1 SandBox;SandBox;c:\windows\system32\drivers\SandBox.sys [2011-1-3 710696]
S2 acssrv;Agnitum Client Security Service;c:\progra~1\agnitum\outpos~1\acs.exe --> c:\progra~1\agnitum\outpos~1\acs.exe [?]
S2 AntiVirSchedulerService;Avira AntiVir Scheduler;c:\program files\avira\antivir desktop\sched.exe [2011-1-3 136360]
S2 AntiVirService;Avira AntiVir Guard;c:\program files\avira\antivir desktop\avguard.exe [2011-1-3 269480]
S2 avgntflt;avgntflt;c:\windows\system32\drivers\avgntflt.sys [2011-1-3 61960]
S2 mrtRate;mrtRate; [x]
S3 afw;Agnitum firewall driver;c:\windows\system32\drivers\afw.sys [2011-1-3 34280]
S3 afwcore;afwcore;c:\windows\system32\drivers\afwcore.sys [2011-1-3 267624]
S3 ASWFilt;ASWFilt;c:\windows\system32\filt\ASWFilt.dll [2011-1-3 72352]
S3 FlyUsb;FLY Fusion;c:\windows\system32\drivers\FlyUsb.sys [2010-1-1 18560]
S3 nosGetPlusHelper;getPlus(R) Helper 3004;c:\windows\system32\svchost.exe -k nosGetPlusHelper [2002-8-29 14336]
S3 VBEngNT;VBEngNT;c:\windows\system32\drivers\VBEngNT.sys [2011-1-3 241088]
S3 VBFilt;VBFilt;c:\windows\system32\filt\VBFilt.dll [2011-1-3 36288]
.
=============== Created Last 30 ================
.
2011-05-28 21:10:14 340480 ----a-w- c:\documents and settings\all users\application data\20963108.exe
2011-05-28 21:00:57 430080 ----a-w- c:\documents and settings\all users\application data\LoBoUYvVYw.exe
2011-05-27 20:22:22 -------- d-----w- c:\windows\CC4C261AB9154F23BD237E1AE5713B4E.TMP
2011-05-14 17:01:39 404640 ----a-w- c:\windows\system32\FlashPlayerCPLApp.cpl
.
==================== Find3M ====================
.
2011-05-15 13:42:14 256 ----a-w- c:\windows\system32\pool.bin
2011-03-07 05:33:50 692736 ----a-w- c:\windows\system32\inetcomm.dll
2011-03-04 06:37:06 420864 ----a-w- c:\windows\system32\vbscript.dll
2011-03-03 13:21:11 1857920 ----a-w- c:\windows\system32\win32k.sys
.
============= FINISH: 11:34:17.42 ===============
Last edited by tashi; 2011-05-29 at 17:44.
Reason: Merged posts
-


Please read Before You Post
While best efforts are made to assist in removing infections safely, unexpected stuff can happen. It is advisable that you back up your important data before starting any clean up procedure. Neither Safer Networking Forums nor the Analyst providing the advice may be held responsible for any loss.
Until we deem your system clean I am going to ask you not to install or uninstall any software or hardware except for the programs we may run.
We need to run RKill, it wont remove anything but will tame the malware so other programs can run
- Please download rkill (Courtesy of Bleepingcomputer.com).
- There are 5 different versions of this tool. If one of them will not run, please try the next one in the list.
- Note: Vista and Windows 7 Users must right click and select "Run as Administrator" to run the tool.
- Note: You only need to get one of the tools to run, not all of them.
- Note: You will likely see a message from this rogue telling you the file is infected. Ignore the message. Leave the message OPEN, do not close the message.
Run rkill repeatedly until it's able to do it's job. This may take a few tries.
You'll be able to tell rkill has done it's job when your desktop (explorer.exe) cycles off and then on again.
Please download TDSSKiller.zip- Extract it to your desktop
- Double click TDSSKiller.exe
- Press Start Scan
- Only if Malicious objects are found then ensure Cure is selected
- Then click Continue > Reboot now
- Copy and paste the log in your next reply
- A copy of the log will be saved automatically to the root of the drive (typically C:\)
Please download Malwarebytes from Here or Here
- Double-click mbam-setup.exe and follow the prompts to install the program.
- At the end, be sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish.
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select Perform quick scan, then click Scan.

- When the scan is complete, click OK, then Show Results to view the results.
- Be sure that everything is checked, and click Remove Selected .
- When completed, a log will open in Notepad. Please save it to a convenient location and post the results.
- Note: If you receive a notice that some of the items couldn't be removed, that they have been added to the delete on reboot list, please reboot.
Post the report please
-
 Step 1
Step 1
I was unable to run the TDS Killer, however I ran the other requested programs. See log from Malwarebytes.
Malwarebytes' Anti-Malware 1.51.0.1200
www.malwarebytes.org
Database version: 6745
Windows 5.1.2600 Service Pack 3 (Safe Mode)
Internet Explorer 8.0.6001.18702
6/1/2011 1:46:31 PM
mbam-log-2011-06-01 (13-46-31).txt
Scan type: Quick scan
Objects scanned: 178953
Time elapsed: 13 minute(s), 10 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 1
Registry Data Items Infected: 1
Folders Infected: 0
Files Infected: 2
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\LoBoUYvVYw (Trojan.FakeMS) -> Value: LoBoUYvVYw -> Quarantined and deleted successfully.
Registry Data Items Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\DisableTaskMgr (PUM.Hijack.TaskManager) -> Bad: (1) Good: (0) -> Quarantined and deleted successfully.
Folders Infected:
(No malicious items detected)
Files Infected:
c:\documents and settings\all users\application data\lobouyvvyw.exe (Trojan.FakeMS) -> Quarantined and deleted successfully.
c:\documents and settings\all users\application data\20963108.exe (Rogue.FakeHDD) -> Quarantined and deleted successfully.
-
-
 aswMBR log
aswMBR log
aswMBR version 0.9.5.256 Copyright(c) 2011 AVAST Software
Run date: 2011-06-01 18:40:54
-----------------------------
18:40:54.859 OS Version: Windows 5.1.2600 Service Pack 3
18:40:54.859 Number of processors: 1 586 0x304
18:40:54.859 ComputerName: TORCHIA UserName: Tim
18:40:56.906 Initialize success
18:40:59.875 Disk 0 (boot) \Device\Harddisk0\DR0 -> \Device\Ide\IdeDeviceP0T0L0-3
18:40:59.906 Disk 0 Vendor: ST340014A 8.16 Size: 38146MB BusType: 3
18:41:01.953 Disk 0 MBR read successfully
18:41:01.953 Disk 0 MBR scan
18:41:01.968 Disk 0 unknown MBR code
18:41:04.000 Disk 0 scanning sectors +78108030
18:41:04.031 Disk 0 scanning C:\WINDOWS\system32\drivers
18:41:13.406 Service scanning
18:41:22.593 Disk 0 trace - called modules:
18:41:22.625 ntoskrnl.exe CLASSPNP.SYS disk.sys >>UNKNOWN [0x81a831ed]<<
18:41:22.640 1 nt!IofCallDriver -> \Device\Harddisk0\DR0[0x81b607f0]
18:41:22.656 3 CLASSPNP.SYS[f9306fd7] -> nt!IofCallDriver -> \Device\Ide\IdeDeviceP0T0L0-3[0x81b1f030]
18:41:22.671 \Driver\atapi[0x81b03eb8] -> IRP_MJ_INTERNAL_DEVICE_CONTROL -> 0x81a831ed
18:41:22.703 Scan finished successfully
18:41:47.015 Disk 0 MBR has been saved successfully to "C:\Documents and Settings\Tim\My Documents\MBR.dat"
18:41:47.046 The log file has been saved successfully to "C:\Documents and Settings\Tim\My Documents\aswMBR.txt"
-

Re-Run aswMBR
Click Scan
On completion of the scan
Click Fix

Save the log as before and post in your next reply
-
 Log from aswMBR
Log from aswMBR
aswMBR version 0.9.5.256 Copyright(c) 2011 AVAST Software
Run date: 2011-06-01 18:40:54
-----------------------------
18:40:54.859 OS Version: Windows 5.1.2600 Service Pack 3
18:40:54.859 Number of processors: 1 586 0x304
18:40:54.859 ComputerName: TORCHIA UserName: Tim
18:40:56.906 Initialize success
18:40:59.875 Disk 0 (boot) \Device\Harddisk0\DR0 -> \Device\Ide\IdeDeviceP0T0L0-3
18:40:59.906 Disk 0 Vendor: ST340014A 8.16 Size: 38146MB BusType: 3
18:41:01.953 Disk 0 MBR read successfully
18:41:01.953 Disk 0 MBR scan
18:41:01.968 Disk 0 unknown MBR code
18:41:04.000 Disk 0 scanning sectors +78108030
18:41:04.031 Disk 0 scanning C:\WINDOWS\system32\drivers
18:41:13.406 Service scanning
18:41:22.593 Disk 0 trace - called modules:
18:41:22.625 ntoskrnl.exe CLASSPNP.SYS disk.sys >>UNKNOWN [0x81a831ed]<<
18:41:22.640 1 nt!IofCallDriver -> \Device\Harddisk0\DR0[0x81b607f0]
18:41:22.656 3 CLASSPNP.SYS[f9306fd7] -> nt!IofCallDriver -> \Device\Ide\IdeDeviceP0T0L0-3[0x81b1f030]
18:41:22.671 \Driver\atapi[0x81b03eb8] -> IRP_MJ_INTERNAL_DEVICE_CONTROL -> 0x81a831ed
18:41:22.703 Scan finished successfully
18:41:47.015 Disk 0 MBR has been saved successfully to "C:\Documents and Settings\Tim\My Documents\MBR.dat"
18:41:47.046 The log file has been saved successfully to "C:\Documents and Settings\Tim\My Documents\aswMBR.txt"
-

Thats the same log from the original scan not the one after the fix
Run aswMBR again, just to scan and post the new log please
-
 2nd log from aswMBR.
2nd log from aswMBR.
Sorry about the resend of the original I could not see the post in the thread, but good now!
aswMBR version 0.9.5.256 Copyright(c) 2011 AVAST Software
Run date: 2011-06-01 20:59:01
-----------------------------
20:59:01.515 OS Version: Windows 5.1.2600 Service Pack 3
20:59:01.515 Number of processors: 1 586 0x304
20:59:01.531 ComputerName: TORCHIA UserName: Tim
20:59:04.078 Initialize success
20:59:14.625 Disk 0 (boot) \Device\Harddisk0\DR0 -> \Device\Ide\IdeDeviceP0T0L0-3
20:59:14.640 Disk 0 Vendor: ST340014A 8.16 Size: 38146MB BusType: 3
20:59:16.687 Disk 0 MBR read successfully
20:59:16.687 Disk 0 MBR scan
20:59:16.703 Disk 0 unknown MBR code
20:59:18.718 Disk 0 scanning sectors +78108030
20:59:18.750 Disk 0 scanning C:\WINDOWS\system32\drivers
20:59:28.656 Service scanning
20:59:36.468 Disk 0 trace - called modules:
20:59:36.484 ntoskrnl.exe CLASSPNP.SYS disk.sys >>UNKNOWN [0x81a831ed]<<
20:59:36.500 1 nt!IofCallDriver -> \Device\Harddisk0\DR0[0x81b607f0]
20:59:36.531 3 CLASSPNP.SYS[f9306fd7] -> nt!IofCallDriver -> \Device\Ide\IdeDeviceP0T0L0-3[0x81b1f030]
20:59:36.546 \Driver\atapi[0x81b03eb8] -> IRP_MJ_INTERNAL_DEVICE_CONTROL -> 0x81a831ed
20:59:36.562 Scan finished successfully
20:59:53.000 Disk 0 MBR has been saved successfully to "C:\Documents and Settings\Tim\My Documents\MBR.dat"
20:59:53.031 The log file has been saved successfully to "C:\Documents and Settings\Tim\My Documents\aswMBR2.txt"
-

Good Morning,
TDSSKiller should run now, run it and post the log.
Download ComboFix from one of these locations:
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools
- See this Link for programs that need to be disabled and instruction on how to disable them.
- Remember to re-enable them when we're done.
- Double click on ComboFix.exe & follow the prompts.
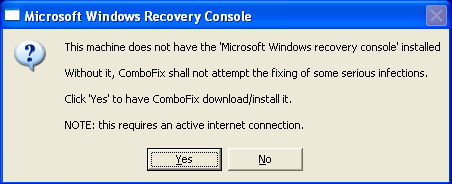
- As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
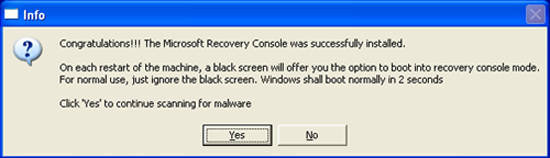
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
*If there is no internet connection when Combofix has completely finished then restart your computer to restore back the connections.
 Posting Permissions
Posting Permissions
- You may not post new threads
- You may not post replies
- You may not post attachments
- You may not edit your posts
-
Forum Rules